The Election Integrity Investigation: EVM Vulnerabilities In USA Between 2015-2025
Why it matters:
- A near-duopoly of three vendors controls over 88% of voting equipment in the U.S., raising concerns about vulnerabilities and lack of federal oversight.
- Documented security flaws and breaches in voting machines highlight the risks of insider threats, physical insecurity, and operational fragility in the election infrastructure.
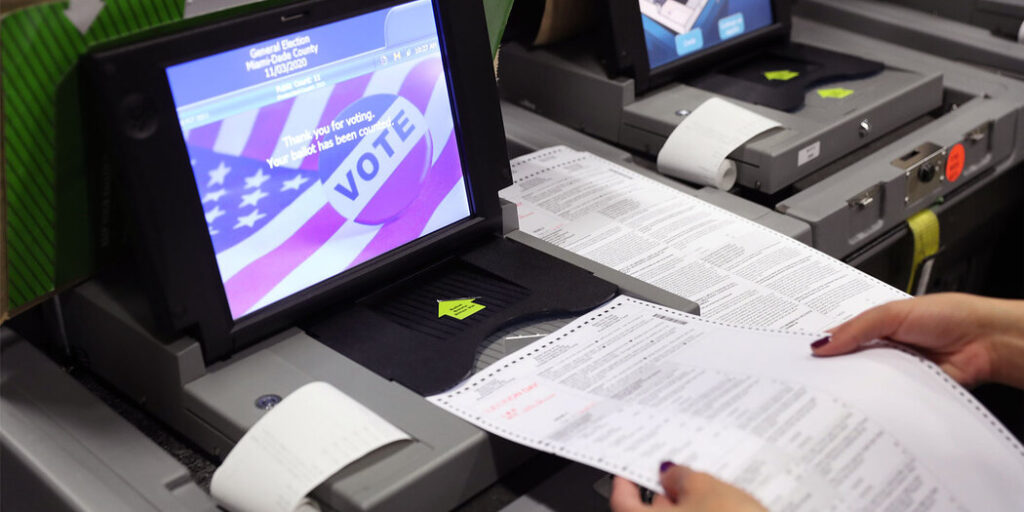
The core of American democracy rests on a foundation of proprietary code and aging hardware, controlled by a near-duopoly that operates with limited federal oversight. As of 2024, three vendors, Election Systems & Software (ES&S), Dominion Voting Systems, and Hart InterCivic, manage the equipment used to count over 88% of all votes cast in the United States. While election officials frequently rule out any kind of EVM vulnerabilities in USA and continue to assert that voting machines are “secure and never connected to the internet,” verified security audits and federal advisories between 2015 and 2025 reveal a different reality: a system with software vulnerabilities, susceptible to insider breaches, and dependent on trust rather than mathematical verification.
In June 2022, the Cybersecurity and Infrastructure Security Agency (CISA) issued an advisory confirming nine specific vulnerabilities in Dominion’s ImageCast X system. These flaws, if left unpatched, allow an attacker with physical access to install malicious code, forge smart cards to print unlimited ballots, and escalate privileges to administrative levels. Similarly, a 2023 analysis of ES&S systems used in 16 states identified serious software weaknesses that could permit local attackers to alter precinct results or erase audit logs. These are not theoretical risks from a sci-fi; they are documented code failures in the machines used by over 100 million voters.
The physical security of this equipment proved equally porous during the chaotic aftermath of the 2020 election. In Coffee County, Georgia, a breach on January 7, 2021, allowed unauthorized individuals to copy proprietary voting software and distribute it to private servers. This event shattered the “security through obscurity” defense frequently by vendors. With the exact code structure in the wild, bad actors possess a blueprint to test attacks against the specific tabulation logic used in Georgia and other states. The breach demonstrated that the greatest threat to election infrastructure frequently comes not from remote hackers, from insider access and physical insecurity.
Operational fragility also poses a serious threat to public confidence. The 2020 Antrim County, Michigan incident, where a failure to update ballot definitions led to a temporary 6, 000-vote error, stands as a clear example. While a hand recount later confirmed the correct results, the initial reporting error, caused by a simple configuration mismatch, fueled years of conspiracy theories. This incident proves that even without malicious intent, the complexity of modern voting systems creates a terrain where human error can produce catastrophic optical failures.
Verified Vulnerabilities and Breaches (2015-2025)
| System / Incident | Date Verified | Nature of Vulnerability | Impact Scope |
|---|---|---|---|
| Dominion ImageCast X | June 2022 | Improper verification of cryptographic signatures; route traversal flaws. | Used in 12+ states; allows arbitrary code execution via physical access. |
| ES&S DS200 / ExpressVote | 2023 | Software flaws allowing audit log deletion and precinct count alteration. | Affects jurisdictions in 16 states; requires access to device ports. |
| Coffee County Breach | Jan 2021 | Unauthorized copying of EMS server and voting software. | Compromised proprietary code security for statewide systems in Georgia. |
| “DVSorder” (CVE-2022-48506) | Nov 2022 | Flawed randomization algorithm in scanners. | Allows public ballot data to be de-anonymized, revealing how individuals voted. |
| DEF CON Voting Village | 2019-2021 | Open USB ports, default passwords, and internal network exposure. | 100% of machines tested were compromised by researchers within hours. |
Even with these findings, the industry has moved slowly to adopt rigorous verification standards. As of 2025, only 15 states require Risk-Limiting Audits (RLAs), the gold standard for detecting tabulation errors. While 99% of U. S. voters live in jurisdictions that produce a paper record, a significant improvement from 2016, the paper trail is useless if states do not mandate hand-to-eye verification of those ballots. The reliance on machine counts without mandatory statistical audits leaves the final verification of power in the hands of the very systems proven to be.
While a nationwide conspiracy to alter votes remains unproven and logistically improbable, the attack surface for local manipulation is wide. The consolidation of vendors, combined with the documented distribution of proprietary software and the slow adoption of RLAs, creates a fragile architecture. We do not need to imagine a grand heist to see the danger; the unlocked doors and broken code are already visible to anyone to look.
The Help America Vote Act: A Catalyst for Rapid Digitization
The Help America Vote Act (HAVA), originally signed in 2002, was intended to modernize American elections after the “hanging chad” debacle of 2000. yet, its long-term legacy, particularly between 2015 and 2025, has been the creation of a fragmented, insecure digital infrastructure. The initial rush to spend federal funds resulted in the widespread adoption of Direct Recording Electronic (DRE) systems, paperless touchscreen machines that, by 2016, had become the single greatest liability in U. S. election security. Instead of a strong upgrade pattern, the decade from 2015 to 2025 became a desperate scramble to replace these aging systems, fueled by sporadic injections of federal cash that frequently deepened vendor lock-in rather than solving structural vulnerabilities.
By the 2016 general election, approximately 28% of registered voters lived in jurisdictions that relied exclusively on paperless DREs. These machines, running on obsolete operating systems like Windows CE or Windows XP, offered no independent method to verify vote totals. The vulnerability of this architecture was not theoretical; it was a mathematical certainty. When the Department of Homeland Security election infrastructure as “serious” in 2017, it triggered a new wave of federal scrutiny, forcing states to confront the reality that their HAVA-funded “upgrades” from the early 2000s were national security risks.
The Second Wave of HAVA Funding (2018, 2024)
In response to confirmed foreign interference attempts, Congress reactivated HAVA funding streams that had been dormant for years. Between 2018 and 2024, the Election Assistance Commission (EAC) distributed approximately $1. 4 billion in “Election Security Funds.” While substantial, this funding was erratic and insufficient to cover the full cost of replacing the nation’s aging fleet of voting machines. State officials were forced to make rapid procurement decisions, frequently prioritizing availability over security architecture, leading to a mass migration from paperless DREs to Ballot Marking Devices (BMDs), systems that produce a paper record still rely on black-box software to interpret voter intent.
| Fiscal Year | Appropriation Amount | Primary Usage Focus |
|---|---|---|
| 2018 | $380 Million | Cybersecurity enhancements, initial DRE replacement |
| 2020 | $425 Million | System upgrades, pandemic response preparation |
| 2022 | $75 Million | Patching security gaps, minor equipment updates |
| 2023 | $75 Million | Maintenance of existing digital infrastructure |
| 2024 | $55 Million | Final pre-election security hardening |
The impact of this funding was uneven. Pennsylvania, under a state mandate to retire paperless machines by the end of 2019, spent approximately $150 million, a mix of federal grants and state bonds, to overhaul its system. The result was a chaotic procurement process where counties rushed to sign contracts with vendors like ES&S and Dominion Voting Systems. Similarly, Georgia utilized its share of federal funds and state appropriations to purchase a $107 million statewide system from Dominion in 2019. This purchase replaced the state’s 27, 000 aging Diebold DREs with BMDs, a move that solved the “paperless” problem introduced new concerns regarding the unverifiable nature of the QR codes these machines use to tabulate votes.
The Decline of Paperless Systems
even with the chaotic implementation, the push to retire paperless DREs achieved measurable results. The percentage of U. S. voters living in jurisdictions with paperless equipment dropped precipitously as states utilized the new HAVA grants. By the 2024 election, Louisiana remained the only state relying entirely on paperless DREs statewide, a situation exacerbated by a multi-year procurement deadlock involving bid protests and allegations of favoritism. In other states, the transition created a hybrid where voters marked paper ballots, the tabulation remained entirely digital and proprietary.
“We replaced one black box with another. The move from paperless DREs to barcode-based Ballot Marking Devices satisfied the requirement for a piece of paper, it did not solve the fundamental problem of software dependence.” , Election Security Analysis, 2023
The financial load of this digitization has fallen heavily on local jurisdictions. While the $1. 4 billion in federal support was significant, the Brennan Center for Justice estimated in 2019 that the cost to replace paperless equipment nationwide would exceed $1 billion for that year alone, not accounting for ongoing maintenance, software licensing, and security audits. Consequently, counties in states like Texas and Tennessee continued to use equipment well past its intended 10-year lifespan, relying on “cannibalized” parts from decommissioned machines to keep their systems operational through the 2020 and 2022 pattern.
This reliance on federal grants created a boom-and-bust pattern for election vendors. Companies like ES&S and Dominion capitalized on the urgent deadlines set by state mandates, securing long-term contracts that frequently included expensive service agreements. The “rapid digitization” catalyzed by HAVA did not result in a standardized, secure federal election system. Instead, it entrenched a private marketplace of proprietary hardware, where security updates are dependent on vendor timelines and public oversight is limited by trade secret laws.
Market Consolidation: The Dominance of the Big Three Vendor Oligopoly
The of American democracy is almost entirely privatized, controlled by a triad of corporations that operate with the opacity of defense contractors without the same level of federal oversight. As of early 2026, three vendors, Election Systems & Software (ES&S), Dominion Voting Systems, and Hart InterCivic, command approximately 88 percent of the United States voting equipment market. This consolidation has created a functional oligopoly where jurisdictions face limited choices, high switching costs, and restrictive contracts that lock taxpayers into proprietary ecosystems for decades.
This market structure is not a matter of limited competition; it represents a fundamental centralization of electoral risk. Unlike public utilities which are subject to strict transparency mandates, these vendors are owned by private equity firms or private investors who are under no legal obligation to disclose their profit margins, executive compensation, or detailed ownership. This financial veil makes it nearly impossible for election officials or the public to trace the flow of money influencing the acquisition of serious voting infrastructure.
The Private Equity Shield
The ownership structures of the “Big Three” shield them from public scrutiny. ES&S is controlled by the McCarthy Group, a private equity firm. Hart InterCivic is majority-owned by H. I. G. Capital. Dominion Voting Systems was long held by Staple Street Capital, the shifted dramatically in October 2025. In a move that alarmed transparency advocates, Dominion was acquired by Liberty Vote, a newly formed entity led by Scott Leiendecker, a former Republican election official. This transaction placed the second-largest voting vendor in the hands of a declared partisan figure, shattering the industry’s long-standing pretense of political neutrality.
| Vendor | Primary Ownership (2026) | Market Position | Notable Contract / Event |
|---|---|---|---|
| Election Systems & Software (ES&S) | McCarthy Group (Private Equity) | #1 (approx. 45-50%) | Secured $51M South Carolina statewide contract (2019); dominant in 2024 pattern. |
| Dominion Voting Systems | Liberty Vote (Scott Leiendecker) | #2 (approx. 30%) | Acquired Oct 2025; holds $107M Georgia statewide contract (10-year term). |
| Hart InterCivic | H. I. G. Capital (Private Equity) | #3 (approx. 15%) | Supplies Verity system to jurisdictions across Texas, Michigan, and others. |
The Mechanics of Vendor Lock-In
Once a jurisdiction selects a vendor, they enter a pattern of dependency known as “vendor lock-in.” The costs to switch systems are prohibitively high, trapping counties with their chosen provider for 10 to 15 years. In 2019, Georgia awarded a $107 million contract to Dominion for a statewide system, a deal that binds the state through 2029 with renewal options. Similarly, South Carolina committed $51 million to ES&S for ballot-marking devices, rejecting lower-cost hand-marked paper ballot alternatives recommended by security experts.
These contracts frequently include “razor-and-blade” provisions. Vendors sell the voting machines, the razors, at a negotiated rate, then charge premium prices for the proprietary ballots, scanners, and annual licensing fees, the blades, required to run them. In Louisiana, a procurement battle raged from 2018 through 2025, with ES&S and Dominion filing successive protests that stalled the replacement of aging machines. The state was left with no viable route to modernize its infrastructure without accepting a nine-figure price tag and a decade-long commitment to a single private entity.
Lobbying and the Absence of Oversight
The oligopoly protects its position through aggressive lobbying. While exact aggregate expenditures are hidden by the private equity structure, specific instances reveal the of influence. In Pennsylvania and Louisiana, vendors have faced scrutiny for lobbying practices that blur the line between education and inducement. ES&S lobbyists in Louisiana, for example, were found to have made campaign donations to election officials, a practice that raises serious ethical questions given the vendors’ reliance on government contracts.
Federal oversight remains toothless. The Election Assistance Commission (EAC) certifies voting systems against voluntary standards absence the authority to regulate the business practices of the vendors themselves. When the House Administration Committee requested details on executive compensation and research and development spending in 2020, the major vendors refused to provide the data, citing their status as private companies. This resistance continues in 2026, leaving the American public with a voting infrastructure that is privately owned, secretly funded, and practically impossible to audit from a financial perspective.
Proprietary Black Boxes: Intellectual Property Laws Blocking Public Oversight
The structural integrity of American elections is currently maintained not by public verification, by the legal enforcement of trade secrets. While the outcome of every race is public record, the software logic that tabulates those results remains the private intellectual property of three private vendors: Election Systems & Software (ES&S), Dominion Voting Systems, and Hart InterCivic. These corporations use a combination of strict non-disclosure agreements (NDAs) and the Digital Millennium Copyright Act (DMCA) to prevent independent security researchers, and even state election officials, from inspecting the source code that powers democracy.
The primary legal barrier is Section 1201 of the DMCA, which criminalizes the circumvention of digital locks on copyrighted software. While the Librarian of Congress granted a limited exemption for “good-faith security research” in 2021, it contains a serious loophole: the research must be conducted on a “lawfully acquired” device. Because vendors restrict the sale of voting machines exclusively to government entities bound by restrictive contracts, independent researchers cannot legally obtain the hardware necessary to test for vulnerabilities. This creates a closed loop where the only entities with access to the machines are contractually prohibited from looking for defects.
The Sealed Evidence: Curling v. Raffensperger
The consequences of this legal opacity were demonstrated in the federal case Curling v. Raffensperger. In July 2021, University of Michigan computer scientist J. Alex Halderman submitted a sealed expert report to the U. S. District Court for the Northern District of Georgia. The report detailed nine specific vulnerabilities in the Dominion ImageCast X system, a machine used by every in-person voter in Georgia and in jurisdictions across 15 other states. Halderman found that attackers could forge smart cards, elevate privileges, and alter vote counts without detection.
Instead of an immediate public warning, the report remained under court seal for nearly two years. The State of Georgia and Dominion Voting Systems argued that releasing the information would compromise election security and expose trade secrets. It was not until June 2022 that the Cybersecurity and Infrastructure Security Agency (CISA) issued an advisory (ICS-Advisory ICSA-22-154-01) validating Halderman’s findings. For eleven months, election officials in other states operated these machines unaware of the serious flaws known to the court, the vendor, and the plaintiffs.
| Component | Public Access Status | Legal/Technical Barrier |
|---|---|---|
| Source Code | Restricted | Classified as “Trade Secret”; access limited to federal certification labs. |
| Hardware Schematics | Restricted | Proprietary vendor IP; protected by patent law and NDAs. |
| Vulnerability Reports | Delayed/Sealed | frequently sealed by courts or redacted under “security” exemptions. |
| Device Ownership | Leased/Licensed | Jurisdictions frequently license software, meaning they do not own the code they use. |
| Independent Audits | Prohibited | DMCA Section 1201 prevents breaking encryption for testing. |
Vendor Litigiousness and Market Control
The major vendors aggressively defend their market position through litigation that prioritizes market share over transparency. In 2018, ES&S sued Cook County, Illinois, after the county attempted to switch to a competitor, delaying the deployment of new technology. Similarly, ES&S and Dominion have engaged in patent infringement lawsuits against one another, such as the 2017 filing where ES&S claimed Dominion’s “ImageCast Evolution” infringed on its patents. These legal battles consume public resources and reinforce a market where proprietary control is the primary asset.
This “black box” model stands in clear contrast to other serious infrastructure sectors. In aviation and cryptography, open peer review is standard practice to ensure safety. In the election sector, yet, “security through obscurity” remains the operating standard. When the code is hidden, errors, whether malicious or accidental, cannot be identified by the public. The 2021 Halderman report proved that serious vulnerabilities can exist for years within certified systems, protected from discovery not by strong encryption, by strong lawyers.
“We discovered vulnerabilities in nearly every part of the system that is exposed to chance attackers… The passwords are not necessary to compromise the equipment.”
, J. Alex Halderman, regarding the Dominion ImageCast X (July 2021)
The refusal to adopt open-source standards means that taxpayers fund the development and purchase of these systems are legally barred from verifying that they work as advertised. Until intellectual property laws are reformed to classify election software as public infrastructure rather than private assets, the method of American democracy remain unverifiable by the people they serve.
The Air Gap Fallacy: Cellular Modems in Precinct Scanners

The most persistent myth in American election security is the concept of the “air gap”, the claim that voting machines are physically from the internet and therefore immune to remote hacking. This defense crumbles under scrutiny of the Election Systems & Software (ES&S) DS200 precinct scanner, the most widely deployed tabulation device in the United States. While vendors and officials frequently repeat the mantra that “voting machines are never connected to the internet,” verified architectural specifications reveal that thousands of these units are equipped with cellular modems designed to transmit “unofficial” election night results. These transmissions the gap between secure polling places and public networks, creating a vector for remote intrusion that computer scientists have warned about for over a decade.
The method of this vulnerability is built into the hardware itself. The DS200 and similar optical scanners frequently house a commercial cellular modem, such as the Multitech MTSMC-C2 series, on their internal circuit boards. On election night, after polls close, poll workers are instructed to plug the machine into a wall outlet or activate the modem to transmit vote totals to a central county server. Vendors describe this as a “brief” and “secure” connection over a “private network.” yet, independent security researchers, including Professor Andrew Appel of Princeton University and Matt Blaze of Georgetown Law, have dismantled these claims. They demonstrate that these “private networks” rely on standard cellular infrastructure (like Verizon or AT&T) using a private Access Point Name (APN). To a sophisticated attacker using a cell-site simulator (commonly known as a Stingray), this traffic is indistinguishable from standard cellular data, making it susceptible to interception and man-in-the-middle attacks.
The “Unofficial Results” Backdoor
The primary justification for these modems is speed: election officials face immense pressure to report results to the media and public immediately after polls close. This convenience introduces a serious security flaw. When a scanner connects to a central server to upload results, the connection is bi-directional. A compromised central server, or a rogue cell tower spoofing the server, can theoretically send malicious commands back to the precinct machine. In 2022, the Cybersecurity and Infrastructure Security Agency (CISA) identified nine vulnerabilities in Dominion Voting Systems’ ImageCast X, a similar class of equipment, confirming that flaws in the software could allow an attacker to install malicious code. While the CISA advisory noted no evidence of exploitation, the mere existence of the route negates the air gap defense.
The distinction between “official” and “unofficial” results is a bureaucratic one, not a technical one. Malware introduced during the “unofficial” transmission window does not once the modem disconnects; it can on the machine’s internal storage, chance altering the “official” paper trail or spreading to other devices during subsequent logic and accuracy testing. A 2023 analysis by the University of Michigan’s J. Alex Halderman demonstrated that attackers could subvert the authentication method of such systems, allowing unauthorized access to administrative functions.
State-Level on Modem Security
The recognition of this threat has led to a fractured regulatory, where the security of a voter’s ballot depends entirely on their state’s specific statutes regarding wireless components. While states have moved aggressively to ban this technology, others have codified its use into law.
| State | Regulatory Status | Policy Details |
|---|---|---|
| Texas | BANNED | Strict prohibition on wireless connections. Texas Election Code § 129. 054 mandates no external network connections. |
| Mississippi | BANNED | 2022 Voting Modernization Act prohibits acquisition of systems with “wireless remote connections.” |
| California | BANNED | Strict “air gap” requirements; voting systems cannot contain modems or connect to public networks. |
| Minnesota | ALLOWED | Statute § 206. 845 explicitly authorizes modems for transmitting unofficial results to central systems. |
| Wisconsin | ALLOWED | Used in multiple jurisdictions for unofficial reporting; subject of ongoing legislative debate legal. |
| Florida | ALLOWED | Certified systems (e. g., DS200) with modems used for rapid reporting; relies on “private network” defense. |
| Michigan | RESTRICTED | Mixed usage; counties use modems for transmission, though security best practices discourage it. |
This regulatory patchwork creates a scenario where a DS200 scanner in Minnesota is legally required to have a modem for speed, while the exact same model in Texas would be illegal if it contained one. The “private network” defense used by states like Florida and Wisconsin relies on the trust that the telecommunications provider (e. g., Verizon) and the vendor (ES&S) maintain perfect security hygiene, a standard that no major technology company has consistently met. In 2024, the Wisconsin Elections Commission reported over 30 referrals for suspected fraud or irregularities, a statistic that, while not exclusively linked to modems, show the fragility of a system dependent on trust rather than verifiable isolation.
“The problem is that the modem talking through the cellphone network really is more connected to the internet than they like to think. Hackers could intercept signals using a portable cell phone tower… [and] are well positioned to alter vote totals.”
, Andrew Appel, Professor of Computer Science, Princeton University
The Cost of Convenience
The financial load of this insecurity is significant. Jurisdictions pay a premium for these modems, frequently hundreds of dollars per unit, and the recurring service fees for the “secure” cellular plans. Public Citizen, a consumer advocacy group, estimated that counties spent nearly $100, 000 solely on modem hardware that actively lowers their security posture. This expenditure prioritizes the 11: 00 PM news pattern over the mathematical certainty of the vote count. By physically connecting the tabulation machine to the world’s most accessible network, election officials trade the “air gap” for a “speed gap,” leaving the sanctity of the precinct count exposed to anyone with the right radio frequency equipment and a motive to disrupt.
Supply Chain Obscurity: Unverified Foreign Component Sourcing
The physical integrity of the American election system rests on a globalized, unclear supply chain that election officials and federal regulators cannot fully audit. While vendors frequently cite “air-gapped” systems as a primary defense against remote hacking, this defense is rendered null if the hardware itself is compromised during manufacturing. Between 2015 and 2025, verified supply chain analyses have demonstrated that a significant percentage of the components inside U. S. voting machines originate from nations with strategic interests in destabilizing American democracy, specifically the People’s Republic of China.
In December 2019, the supply chain risk management firm Interos released a forensic analysis of a widely used voting machine model. The findings dismantled the industry’s claims of secure, domestic manufacturing. The audit revealed that 20% of the machine’s hardware and software components came from China-based companies. also, the investigation found that 59% of the suppliers in the three tiers of the supply chain had locations in China or Russia. These components included serious infrastructure elements such as control boards, AI processors, and touchscreens, the very nervous system of the voting apparatus.
The “Black Box” of Hardware Manufacturing
The primary vendors, Election Systems & Software (ES&S), Dominion Voting Systems, and Hart InterCivic, operate under a proprietary model that treats their Hardware Bill of Materials (HBOM) as a trade secret. This commercial secrecy prevents independent security researchers and the public from verifying exactly what is inside the machines used to count votes. During a January 2020 congressional hearing, executives from all three major vendors admitted under oath that they rely on Chinese components. Dominion CEO John Poulos testified that for certain parts, such as glass screens and capacitors, there is “no option” other than manufacturing in China.
This reliance creates a specific vulnerability known as “supply chain interdiction.” Intelligence agencies have long warned that adversaries can tamper with hardware during the manufacturing or shipping process, embedding “backdoors” or malicious microchips that are undetectable by standard software audits. A compromised capacitor or logic board can be triggered to alter machine behavior under specific conditions, bypassing the software security checks that election officials rely upon.
| Component Tier | Origin Risk Factor | Verified Findings |
|---|---|---|
| Tier 1 (Direct Suppliers) | High | Major sub-assemblies sourced from vendors with manufacturing hubs in Shenzhen and Shanghai. |
| Tier 2 & 3 (Raw Components) | serious | 59% of suppliers have operations in China or Russia; components include programmable logic devices and LCDs. |
| Final Assembly | Moderate | “Made in USA” labels frequently refer only to the final screwdriver assembly of pre-manufactured foreign kits. |
The Illusion of Regulatory Oversight
Federal oversight has failed to close this security gap. The Election Assistance Commission (EAC) adopted the Voluntary Voting System Guidelines (VVSG) 2. 0 in February 2021, which included updated supply chain risk management standards. yet, these guidelines are voluntary for states and non-retroactive. For the 2024 general election, the vast majority of jurisdictions deployed legacy equipment certified under older standards (VVSG 1. 0 or 1. 1) that did not require granular supply chain transparency. Consequently, the machines used in 2024 contained the same unverified foreign components identified in the 2019 Interos report.
The Cybersecurity and Infrastructure Security Agency (CISA) has issued general guidance on “Supply Chain Risk Management” (SCRM), it absence the statutory authority to ban specific foreign components in state-purchased voting systems. Unlike the telecommunications sector, where the FCC has banned equipment from Huawei and ZTE due to national security risks, the election technology sector faces no such federal prohibition on Chinese hardware. This regulatory blind spot allows vendors to prioritize cost-efficiency over national security, sourcing cheap microelectronics from adversarial nations without public disclosure.
The Persistence of Opacity
As of 2025, no major voting machine vendor has released a full, public Hardware Bill of Materials for their flagship tabulators. The “trust us” model remains the industry standard. When pressed on supply chain security, vendors point to internal audits and “acceptance testing” by local officials. Yet, local election officials absence the specialized equipment, such as electron microscopes or x-ray imaging tools, required to detect hardware-level tampering. They verify that the machine turns on and counts a test deck, not that the motherboard is free of rogue microchips.
This absence of verification transforms the voting machine from a public utility into a proprietary black box. Without a transparent, auditable chain of custody for every resistor and processor, the assertion that American elections are secure from foreign hardware interference remains a statement of faith, not a verified fact.
Physical Security Failures: Commercial Locks and Unrestricted Port Access
The assumption that electronic voting machines are secure because they are “air-gapped” or not connected to the internet crumbles upon physical inspection. Between 2015 and 2025, security researchers and federal audits repeatedly demonstrated that the physical blocks protecting these devices are frequently little more than “security theater.” The most worrying failures involve the use of generic, mass-produced keys for sensitive access panels and the presence of unrestricted data ports that allow bad actors to bypass software safeguards entirely. In documented cases, the physical locks protecting the “crown jewels” of American democracy, the vote tabulation hard drives and memory cards, can be opened with keys available for purchase on Amazon or eBay for less than $10.
The “CH751” Problem: Universal Keys for serious Infrastructure
A foundational failure in voting machine security is the reliance on standard commercial locks. Security audits from the DEF CON Voting Village and independent state reviews have confirmed that vendors frequently use the CH751 and C415A key series for cabinet locks on voting equipment. These keys are not unique to election hardware; they are the industry standard for camper shells, office furniture, and janitorial supply cabinets. An attacker does not need high-level clearance to open these machines; they simply need a key that millions of Americans already have on their keychains.
During the 2018 and 2019 DEF CON Voting Village events, researchers breached the physical security of an ES&S M650 high-speed tabulator in under one minute. The machine, used to count absentee ballots in multiple states, was opened using a standard key, exposing its internal electronics. Once inside, the absence of chassis intrusion detection systems meant that an attacker could tamper with the hardware or insert malicious media without leaving a digital trace. This vulnerability is not theoretical; it is a structural flaw in the supply chain of election hardware.
Unrestricted Port Access and the “Bash Bunny” Threat
Beyond weak locks, the external ports on voting machines, specifically USB and Ethernet ports, serve as open doors for malicious code. In June 2022, the Cybersecurity and Infrastructure Security Agency (CISA) issued ICS Advisory ICSA-22-154-01, confirming nine serious vulnerabilities in the Dominion ImageCast X system. The advisory explicitly stated that an attacker with physical access could “install malicious code” or “escalate privileges” by connecting an external device. This vulnerability allows for the execution of arbitrary code, chance altering vote tallies or disabling the machine entirely.
The “Halderman Report,” unsealed by a federal court in June 2023, detailed how these port vulnerabilities could be exploited in Georgia’s election system. Professor J. Alex Halderman demonstrated that a simple USB device could be used to reboot the machine into “Android Safe Mode,” bypassing the kiosk software that restricts voters to the ballot interface. Once in Safe Mode, an attacker has full administrative control over the device. Similarly, at DEF CON, researchers used a “Bash Bunny”, a commercially available USB attack tool, to automate the injection of payloads into voting machines, compromising them in seconds.
Verified Physical Vulnerabilities by Model (2015-2025)
The following table aggregates verified physical security failures from federal advisories and independent security audits.
| Machine Model | Vendor | Physical Vulnerability | Source / Year |
|---|---|---|---|
| ImageCast X | Dominion | USB port allows reboot to Android Safe Mode; arbitrary code execution. | CISA ICSA-22-154-01 (2022) |
| DS200 | ES&S | Unencrypted Compact Flash file system; exposed USB ports. | DEF CON 25 Report (2017) |
| M650 | ES&S | Cabinet lock picked in <1 minute; internal serial port access. | DEF CON 26 Report (2018) |
| eSlate | Hart InterCivic | Exposed ports allowed daisy-chain attacks on connected peripherals. | Verified Voting / CA Audit (2019) |
| WinVote | AVS | Hardcoded WEP Wi-Fi password; “admin” default password. | Virginia State Audit (2015) |
Visualizing the Attack Surface
The that physical access points, ports and locks, constitute the primary vector for local attacks. The chart illustrates the distribution of physical vulnerability types identified across major voting system audits between 2017 and 2024.
Primary Physical Attack Vectors (2017-2024 Audits)
Source: Aggregated data from DEF CON Voting Village Reports & CISA Advisories
The persistence of these vulnerabilities highlights a widespread negligence in the design phase of election hardware. Manufacturers prioritize ease of maintenance, using common keys and standard ports, over the hardening required for serious infrastructure. While CISA and vendors that “physical security procedures” by poll workers mitigate these risks, the reality of a busy polling place makes 100% vigilance impossible. A distraction of ten seconds is all a prepared attacker needs to insert a USB drive or open a cabinet, rendering the software security of the machine irrelevant.
Direct Recording Electronic Systems: The Dangers of Paperless Voting
The Direct Recording Electronic (DRE) voting machine represents the most unclear chapter in American election technology. Unlike optical scanners that count physical paper ballots, DREs record votes directly into computer memory. There is no software-independent record of the voter’s intent. If the machine’s memory fails, or if malicious code alters the tally, the truth. As of 2024, approximately 3. 9% of registered voters in the United States still live in jurisdictions that rely on these “black box” systems, primarily in Louisiana and parts of Texas. The refusal to abandon this technology creates a persistent security gap that no amount of pre-election testing can close.
The “Black Box” Problem
The fundamental flaw of the DRE is its architecture. In a paper-based system, the ballot is the primary record; the scanner is a tool to count it. In a DRE system, the computer is the judge, jury, and executioner. Security researchers at DefCon’s Voting Village have repeatedly demonstrated the fragility of these systems. In 2018 and 2019, hackers successfully compromised the ES&S iVotronic, a common DRE model. They exploited buffer overflows and weak passwords to escalate privileges, theoretically allowing an attacker to alter vote tallies or disable machines across a precinct. These are not hypothetical risks; they are documented technical realities that exist in hardware still deployed in American elections.
“The DREs used in Georgia do not produce a voter-verifiable paper record… The accuracy of DRE results cannot be checked.”
, Curling v. Raffensperger, U. S. District Court Ruling (2019)
The Georgia “Smoking Gun”: 160, 000 Missing Votes
The most damning evidence against DREs emerged from the 2018 Georgia Lieutenant Governor’s race. While the Governor’s race between Brian Kemp and Stacey Abrams drew national attention, a statistical anomaly occurred down-ballot. In the contest between Geoff Duncan and Sarah Riggs Amico, approximately 160, 000 votes, nearly 4% of the total, simply disappeared. These “undervotes” appeared almost exclusively on the state’s paperless DRE machines. In contrast, absentee mail ballots (which are paper) showed an undervote rate of less than 1%.
Data scientists and election integrity experts concluded that the machines likely suffered from a user interface failure or a calibration error that caused voters to miss the race entirely or the machine to fail to record their selection. Because there were no paper ballots to recount, the 160, 000 missing votes remained a mystery, and the election results stood. This incident directly influenced the federal court ruling in Curling v. Raffensperger, which forced Georgia to abandon DREs in favor of Ballot Marking Devices (BMDs) with paper trails.
The “Vote Flipping” Phenomenon
Voters frequently report that DRE touchscreens “flip” their votes, selecting a Republican when they pressed Democrat, or vice versa. In the 2018 Texas midterms, voters in 82 counties using Hart InterCivic eSlate machines reported that the “straight-ticket” selection wheel switched their U. S. Senate vote. The Secretary of State attributed this to “user error,” claiming voters spun the selection wheel too fast for the screen to render. Whether caused by hardware lag, calibration drift, or software bugs, the result is the same: the voter loses confidence in the system. In a paperless environment, the voter has no way to prove the machine erred, and officials have no way to prove it didn’t.
The Final Holdouts: Louisiana and Texas
While most of the nation has moved to paper, a few jurisdictions remain dangerously behind. Louisiana stands as the only state to use paperless DREs statewide in 2024. The state’s procurement process for new machines has been mired in delays, legal battles, and funding disputes, with a full replacement pushed to 2026. The estimated cost to replace Louisiana’s aging fleet exceeds $100 million. In Texas, a 2021 law mandates that all counties transition to systems with a paper trail by 2026, yet several counties continued to use paperless DREs in the 2024 election pattern.
| State | Equipment Status | Replacement Deadline | Key Risk Factor |
|---|---|---|---|
| Louisiana | Statewide use of paperless DREs (Dominion/Sequoia) | 2026 (Delayed) | Zero auditability; aging hardware failure |
| Texas | Used in select counties (e. g., Limestone, Foard) | 2026 (Mandated by Law) | “Vote flipping” reports; calibration drift |
| Indiana | Hybrid use; moving to VVPAT | 2024-2025 | VVPAT printer jams; difficult verification |
The Failure of VVPATs
jurisdictions attempted to salvage their DRE investment by adding Voter Verified Paper Audit Trails (VVPATs). These are small thermal printers, similar to cash register receipt printers, attached to the DRE. They present a “toilet paper” trail of the vote behind a glass window. While better than nothing, VVPATs are a flawed stopgap. They frequently jam, run out of paper, or print illegible text. most voters do not verify the text on the thermal tape, rendering the “verification” aspect void. also, auditing a continuous roll of thermal paper is logistically difficult compared to counting individual ballot cards.
The era of the paperless vote is ending, it is not over. Until every DRE is retired, American elections retain a vulnerability that no amount of cybersecurity can fix: the inability to prove, with physical evidence, that the winner actually won.
The Barcode gap: When Human Eyes Cannot Verify the Count
The fundamental pledge of the voter-verified paper audit trail (VVPAT) is that the voter can confirm their choices before casting a ballot. yet, for millions of Americans voting on Ballot Marking Devices (BMDs), this pledge is technically illusory. Machines such as the ES&S ExpressVote and Dominion ImageCast X produce a paper record containing two distinct data streams: a human-readable text summary and a machine-readable barcode (or QR code). In these configurations, the tabulator scans and counts only the barcode. The human text serves as a receipt, one that the counting machine ignores entirely.
This architecture creates a “verification gap.” If malware or a configuration error causes the machine to print the correct candidate name in text encodes a different candidate in the barcode, the gap is invisible to the voter. The vote is cast for the wrong candidate, and the voter leaves the booth believing they verified their ballot. This is not a theoretical risk; it is a documented architectural vulnerability confirmed by federal security advisories.
The 6. 6% Verification Reality
Election officials frequently that voters can protect themselves by checking the printed text. Research proves this safeguard is statistically ineffective. A landmark 2020 study by the University of Michigan conducted a mock election with 241 participants using compromised BMDs. The machines were programmed to deliberately alter one vote on every printed ballot. The results were clear: only 40% of voters reviewed their printed ballots at all. Of those who did, the vast majority failed to notice the error. In total, only 6. 6% of participants told a poll worker that their ballot was incorrect.
This that in a real-world scenario, a machine altering 100 votes would likely be caught by fewer than seven voters, a margin of error easily dismissed as voter confusion rather than widespread fraud.
| Voter Action | Percentage of Participants | Implication |
|---|---|---|
| Reviewed Ballot | 40. 0% | Majority of voters cast ballots blindly. |
| Detected Error | 6. 6% | Malicious alterations go 93. 4%. |
| Reported to Official | 6. 6% | widespread fraud mimics user error. |
The “Split-Brain” Failure: Northampton County 2023
The danger of separating text from tabulation data materialized in Northampton County, Pennsylvania, during the November 2023 election. Voters using ES&S ExpressVote XL machines noticed that the printed text on their ballots had flipped the retention votes for two Superior Court judges. A “Yes” vote on the screen printed as “No” on the paper summary, and vice versa. County officials and ES&S later confirmed this was a coding error.
While officials insisted the barcodes were correct and would have tallied the votes accurately, the incident demonstrated the “split-brain” nature of BMDs. The text and the code are generated by different software processes. In Northampton, the text was wrong, and the code was (reportedly) right. In a malicious attack, a hacker would invert this: the text would be correct to satisfy the voter, while the barcode would be wrong to rig the count. Because the scanner reads only the barcode, the fraudulent count would become the official result, and the paper trail, unless subjected to a rigorous hand audit, would affirm the fraud.
Federal Confirmation and Legislative Bans
In June 2022, the Cybersecurity and Infrastructure Security Agency (CISA) released an advisory (ICS-Advisory ICSA-22-154-01) confirming vulnerabilities in Dominion Voting Systems ImageCast X. The advisory noted that an attacker could “use” (exploit) these flaws to install malicious code, chance altering the QR codes printed on ballots. This federal acknowledgment validated the concerns of security researchers like J. Alex Halderman, who had demonstrated similar attacks in court proceedings.
Recognizing this security hole, several states have moved to ban barcodes entirely. Colorado Secretary of State Jena Griswold prohibited the certification of voting systems that tabulate from barcodes, requiring a transition to full-text optical character recognition (OCR) or darkened ovals. In 2024, the Tennessee legislature passed a bill banning QR codes on ballots, mandating that vote tabulators must read the human-readable text. These legislative actions reflect a growing consensus that a voting system cannot be secure if the voter cannot verify the specific data element that the machine counts.
“The barcode is the vote. The text is just a receipt. If the voter cannot read the barcode, they are not verifying their vote; they are verifying a receipt that the machine is free to ignore.”
The industry reliance on barcodes prioritizes machine efficiency over transparency. While vendors that barcodes prevent ambiguity in scanning, they introduce an opacity that breaks the chain of custody between the voter’s intent and the tabulated result. Until scanners are required to read the same text the voter verifies, the “voter-verified” paper trail remains a partial misnomer.
Memory Card Vectors: Injecting Malicious Payloads via Removable Media

The prevailing defense offered by election officials regarding voting machine security is the “air gap”, the assertion that because machines are not directly connected to the public internet, they are immune to cyberattacks. This defense collapses when examining the operational need of removable media. To function, voting machines require programming via memory cards or USB drives generated by a central Election Management System (EMS). These same cards are later used to transport vote tallies back to the central tabulator. This “sneaker-net” architecture creates a high-risk physical between the central system and the distributed fleet of voting terminals, turning standard administrative procedures into viable attack vectors.
Between 2015 and 2025, security researchers and federal agencies confirmed that this data transfer method serves as a primary entry point for malicious payloads. In a landmark advisory issued on June 3, 2022, the Cybersecurity and Infrastructure Security Agency (CISA) validated nine serious vulnerabilities in Dominion Voting Systems’ ImageCast X equipment. The advisory (ICSMA-22-154-01) explicitly stated that an attacker with physical access to the device or the ability to modify files before upload could “escalate privileges” and “install malicious code.” This finding dismantled the assumption that the machines are secure simply because they are offline.
The “Viral” Propagation method
The most severe threat identified in recent forensic analyses is the chance for “viral” malware propagation. In a detailed security analysis unsealed in 2023, University of Michigan computer scientist J. Alex Halderman detailed how an infection could originate at the county’s central EMS and spread to every voting machine in the jurisdiction. The attack vector relies on the election definition files, data packages loaded onto USB sticks to program the ballot styles for each precinct.
Halderman’s team demonstrated that malicious code could be within these election definition files. When a poll worker inserts the infected USB drive into a voting machine to initialize it for the election, the machine reads the file, triggers a vulnerability (such as a buffer overflow), and executes the malicious payload. This process requires no internet connection and can occur during standard pre-election logic and accuracy testing or on Election Day setup. Once the machine is compromised, the malware can alter vote counts, disable the device, or modify the printed ballots.
| System Component | Vulnerability Type | Impact | Source |
|---|---|---|---|
| Dominion ImageCast X | Improper Verification of Update Files | Allows installation of malicious code via USB during boot or update. | CISA Advisory ICSMA-22-154-01 (2022) |
| ES&S AutoMARK | Unauthenticated Boot | Device boots from USB without password, granting root access. | DEF CON Voting Village Report (2019) |
| Optical Scanners (Generic) | Memory Card Manipulation | Remote manipulation of memory card data when scanner connects to network. | DEF CON Voting Village (2019) |
| Election Management System | Viral Propagation | Malware spreads from EMS to fleet via election definition media. | Halderman Security Analysis (2021/2023) |
The Fallacy of Physical Security
Vendors and officials frequently that strict physical chain-of-custody procedures prevent these attacks. This argument presumes that bad actors cannot gain physical access to the equipment. yet, the breach in Coffee County, Georgia, on January 7, 2021, serves as a documented counterexample. In that incident, unauthorized individuals were granted sustained access to the county’s election server and voting equipment. Forensic teams copied the proprietary software and hard drive images, obtaining the “keys to the kingdom.”
With exact copies of the voting system software, adversaries can study the code in a lab environment to identify zero-day vulnerabilities and craft exploit payloads specifically designed for the memory cards used in that jurisdiction. The Coffee County breach demonstrated that the “physical barrier” is permeable when insider threats or unauthorized access occur. Once the software is reverse-engineered, an attacker can create a weaponized memory card that looks identical to a legitimate one.
Technical Execution of the Attack
The technical mechanics of these attacks frequently exploit the absence of cryptographic signing or insufficient validation of input data. In legacy systems still in use as of 2024, the voting machine operating system mounts the USB drive or memory card automatically upon insertion. If the machine’s software does not rigorously sanitize the data on the card, a malformed file name or a specific binary sequence can cause the system to crash or execute arbitrary code. At the DEF CON Voting Village in 2023, researchers demonstrated the use of “Bash Bunny” USB devices, commercial penetration testing tools, to deploy payloads into voting machines, scrambling tallying capabilities within seconds of insertion.
The reliance on commercial off-the-shelf (COTS) components, such as standard USB ports and Windows or Android operating systems, further lowers the barrier for entry. Unlike bespoke hardware that requires specialized knowledge, these interfaces are well-understood by the broader hacking community. The convergence of known operating system vulnerabilities with the specific absence of hardening in voting machine software creates a fertile ground for exploitation via removable media.
The Insider Threat: Elevated Privileges and Unmonitored Admin Access
The most sophisticated firewall cannot stop an attacker who has the keys to the server room. While external cyber threats dominate public discourse, verified security audits and federal advisories from 2015 to 2025 demonstrate that the most immediate danger to election system integrity frequently comes from within. The architecture of modern voting systems, specifically those manufactured by Election Systems & Software (ES&S) and Dominion Voting Systems, relies heavily on “administrative access” privileges that, once granted, frequently allow users to bypass security, disable logging method, and alter serious data without immediate detection.
On June 3, 2022, the Cybersecurity and Infrastructure Security Agency (CISA) released an advisory (ICS-Advisory ICSA-22-154-01) confirming nine specific vulnerabilities in the Dominion ImageCast X system. The advisory explicitly stated that an attacker with physical access and administrative privileges could “install malicious code” or “escalate privileges” to take control of the device. Crucially, CISA noted that exploiting these flaws required access to the Election Management System (EMS), the central server used to program every voting machine in a county. This advisory moved the concept of an “insider threat” from theoretical possibility to a verified government warning.
The Mechanics of Unchecked Authority
The core problem lies in the design of administrative access. In jurisdictions, “admin” accounts are not tied to individual users with multi-factor authentication are instead shared generic logins (e. g., “admin” or “administrator”) used by multiple election staff and contractors. A 2022 analysis by the University of Michigan and verified by CISA findings showed that once a user logs in with these elevated privileges, they frequently possess the ability to modify the very audit logs that are supposed to record their actions.
| Jurisdiction | Date of Breach | Method of Access | Detection Latency |
|---|---|---|---|
| Mesa County, CO | May 2021 | Elected Official (Clerk) disabled cameras; used badge to grant entry. | 3 Months (Detected via external leak) |
| Coffee County, GA | Jan 2021 | Election Supervisor invited unauthorized forensics team to copy EMS server. | 18 Months (Detected via civil lawsuit discovery) |
| Antrim County, MI | Nov 2020 | Unauthorized imaging of EMS server by private entities. | Detected post-audit |
The danger of this unmonitored access was proven in Mesa County, Colorado. In May 2021, County Clerk Tina Peters facilitated a security breach by allowing unauthorized individuals to access the secure server room during a software update known as a “trusted build.” Court records from her 2024 conviction reveal that Peters ordered security cameras to be turned off prior to the breach. The unauthorized operatives created forensic images of the election server, capturing proprietary software and passwords. The system itself did not trigger an alarm; the breach was only discovered in August 2021 when the stolen passwords were posted publicly on the messaging app Telegram. The voting system’s internal security measures failed to detect the exfiltration of its own hard drive because the attack was authorized by a valid administrative credential.
The Coffee County Breach: A Case Study in Silent Access
A similar more prolonged failure occurred in Coffee County, Georgia. On January 7, 2021, a team of computer forensics experts was granted access to the county’s elections office by local election supervisor Misty Hampton. Surveillance video, which only surfaced publicly in 2022, shows the team spending hours inside the secure area, copying data from the Election Management System server and ballot scanners.
This breach went by state officials for over a year. The Georgia Secretary of State’s office, which manages the statewide voting system, had no real-time monitoring capability to see that the Coffee County server was being accessed and imaged by unauthorized devices. The breach was not flagged by the Dominion software or the operating system logs because the access was facilitated by an insider with valid keys and codes. It took civil litigation, not automated security alerts, to uncover the fact that the state’s proprietary election software had been compromised and distributed to unauthorized parties.
widespread Vulnerabilities in Audit Logging
The inability to detect these breaches in real-time points to a serious flaw in the audit logging architecture. In a high-security environment, such as a bank or a nuclear facility, administrative actions are logged to a remote, immutable server (a “write-once” drive) that the administrator cannot access. In contrast, election systems store audit logs locally on the same machine that the administrator controls.
“The authentication method used by technicians… is susceptible to forgery. An attacker with physical access may use this to gain administrative privileges on a device and install malicious code or perform arbitrary administrative actions.”
, CISA Advisory ICSA-22-154-01 (June 3, 2022)
When an insider has “root” or administrative access, they possess the digital authority to clear event logs or modify the database that tracks user activity. A 2023 report by the Coalition for Good Governance highlighted that in the Coffee County incident, the absence of immutable, off-site logging meant that investigators had to rely on physical building security cameras to reconstruct the timeline of the breach, rather than digital forensic trails which were either incomplete or insufficient.
The industry’s reliance on “air-gapping”, keeping machines disconnected from the internet, paradoxically aids the insider threat. Because the machines are not connected to a central security operations center (SOC), there is no live telemetry to warn state officials if a server in a rural county is being accessed at 2: 00 AM or if its entire hard drive is being copied. Security relies entirely on the physical loyalty of the local custodian. As demonstrated in Colorado and Georgia, when that loyalty fractures, the digital locks on the ballot box are rendered useless.
Certification Bottlenecks: The Multi-Year Lag in VVSG Standards
The federal certification process for voting systems operates on a timeline that is dangerously out of sync with the pace of modern cybersecurity threats. While the Election Assistance Commission (EAC) unanimously adopted the Voluntary Voting System Guidelines (VVSG) 2. 0 in February 2021, the actual deployment of compliant technology has faced a paralysis lasting nearly half a decade. As of December 2025, the vast majority of voting machines in the United States continue to run on software certified to VVSG 1. 0, standards originally drafted in 2005, two years before the release of the iPhone.
This lag is not bureaucratic; it represents a fundamental security gap. VVSG 2. 0 introduced serious requirements for “software independence,” banning the wireless modems and complex connectivity features that have plagued earlier systems. Yet, for the entire 2024 presidential election pattern, zero votes were cast on VVSG 2. 0-certified equipment. The system to achieve this standard, Hart InterCivic’s Verity Vanguard 1. 0, did not receive federal certification until July 7, 2025, four years and five months after the standards were approved.
The Vendor Submission Vacuum
The bottleneck is exacerbated by the slow submission rates of the industry’s dominant vendors. even with the urgent need for updated security, major manufacturers delayed submitting their flagship systems for VVSG 2. 0 testing until late 2025. This delay guaranteed that the 2024 election would be conducted on legacy infrastructure.
| Vendor | System Name | Submission Date | Certification Status |
|---|---|---|---|
| Hart InterCivic | Verity Vanguard 1. 0 | 2022 (Testing Start) | Certified (July 7, 2025) |
| Dominion (Liberty Vote) | Frontier 1. 0 | November 2025 | Under Test (Expected late 2026) |
| ES&S | EVS 6. 4. 0. 0 (VVSG 2. 0 Release) | December 15, 2025 | Under Test |
| Unisyn | Optio Voting System 1. 0 | October 7, 2025 | Under Test |
The data reveals a clear reality: Election Systems & Software (ES&S) and Dominion Voting Systems ( rebranded as Liberty Vote), which together control over 70% of the U. S. market, did not have a VVSG 2. 0 system in the testing pipeline during the 2024 election. Instead, these vendors relied on “de minimis” changes, minor updates to existing VVSG 1. 0 systems that allow them to bypass full recertification. This loophole permits aging software architectures to remain in use indefinitely, receiving only superficial patches rather than the structural security overhauls required by VVSG 2. 0.
Regulatory Whiplash and Executive Order 14248
The certification pipeline was further complicated by shifting federal requirements. In March 2025, Executive Order 14248 was issued, mandating that voting systems must not use barcodes or QR codes for vote counting, except to accommodate disabilities. This directive forced vendors to re-engineer systems mid-development, contributing to the late 2025 submission flurry.
The friction between the EAC’s voluntary guidelines and new executive mandates created a compliance quagmire. Vendors argued that the “massive overhaul” required by VVSG 2. 0, which demands complete software independence and bans cost-saving commercial-off-the-shelf (COTS) components, made rapid upgrades financially impractical. Consequently, election officials were left with no choice to purchase and deploy VVSG 1. 0 legacy systems, locking jurisdictions into outdated security standards for another 10 to 15 years.
“The brave 2023 buyers or the early adopters in 2025… pave the way for a more general refresh of voting technology across the country in 2026 or 2027. This also means that voting systems designed to the new VVSG 2. 0 standard are likely to still be in use in jurisdictions around 2040.” , OSET Institute Analysis on VVSG Lifecycles
This “certification lag” creates a permanent window of vulnerability. While VVSG 2. 0 standards mandate air-gapped systems, integrity checks, and multi-factor authentication, the machines actually tallying votes in 2024 operated without these federally recommended safeguards. The reliance on the “de minimis” process has grandfathered in vulnerabilities that the EAC’s own new standards were designed to eliminate.
The Gatekeepers for Hire: Private Labs and the “Pay-to-Play” Certification Model
The federal certification of voting systems in the United States is not conducted by government scientists or independent academic institutions. Instead, this serious national security function is outsourced to two private, for-profit companies: Pro V&V in Huntsville, Alabama, and SLI Compliance in Wheat Ridge, Colorado. These two entities form a duopoly that acts as the sole gatekeeper for nearly every vote cast in America. The structural flaw in this arrangement is absolute: voting machine manufacturers, Election Systems & Software (ES&S), Dominion, and Hart InterCivic, pay these laboratories directly to test and approve their products. This “client-vendor” relationship creates a financial conflict of interest where the entity seeking certification funds the entity granting it.
Unlike the pharmaceutical industry, where the FDA conducts independent reviews of data, the Election Assistance Commission (EAC) relies almost exclusively on the test reports generated by these vendor-paid labs. Between 2015 and 2025, Pro V&V and SLI Compliance certified systems that were later found to contain serious security vulnerabilities by independent researchers. The labs operate with minimal transparency; as private corporations, they are not subject to the same Freedom of Information Act (FOIA) requirements as federal agencies, shielding their internal financial structures and specific testing from public scrutiny.
The “De Minimis” Loophole: Bypassing Security Checks
One of the most worrying method in the certification process is the “de minimis” change determination. This regulatory loophole allows manufacturers to modify certified voting systems without undergoing a full new round of security testing if the lab deems the change “minor.” In the lead-up to the 2024 election, Pro V&V approved a software modification for ES&S systems (ECO 1188) as a de minimis change. This determination allowed the update to be deployed across multiple jurisdictions without the rigorous federal testing pattern required for a new system. Critics and election integrity advocates argued that this “rubber stamp” method introduced unverified code into the election ecosystem mere months before voting began, bypassing the safeguards intended to prevent supply chain attacks.
Case Study: The Halderman Report vs. Lab Certification
The between lab certification and actual security reality was clear exposed in the case of Curling v. Raffensperger in Georgia. Pro V&V had certified the Dominion ImageCast X (ICX) ballot-marking devices as secure and compliant with federal voluntary voting system guidelines (VVSG). Yet, a sealed expert report by University of Michigan computer scientist J. Alex Halderman, released to the public in June 2023, identified nine “serious vulnerabilities” in the same specific software version.
Halderman’s analysis demonstrated that an attacker could install malicious software to alter vote counts by exploiting flaws that the accredited lab had either missed or deemed acceptable. The lab’s testing protocol failed to identify that the system’s barcode generation method could be manipulated to print votes different from what the voter selected on the screen. This failure highlights a catastrophic gap in the VSTL (Voting System Test Laboratory) methodology: the labs test for compliance with outdated checklists, while independent security experts test for actual exploitability against modern threats.
| System Component | Accredited Lab Finding (Pro V&V / SLI) | Independent Expert Finding (CISA / Halderman) | Outcome |
|---|---|---|---|
| Dominion ImageCast X | Certified “Compliant” (Pro V&V) | 9 serious Vulnerabilities; Susceptible to arbitrary code execution | CISA issued advisory ICS-MA-22-154-01 requiring patches. |
| ES&S DS200 (ECO 1188) | Approved “De Minimis” Change (Pro V&V) | Untested for new attack vectors introduced by modification | Deployed in 2024 election without full re-certification. |
| Maricopa Tabulators (2020) | Audited “Secure” (Pro V&V & SLI) | Log files showed unverified admin access (Independent Review) | Labs confirmed their own prior certification work during audit. |
Ownership and Accreditation Gaps
The corporate structures of the labs themselves raise further questions. SLI Compliance is a division of Gaming Laboratories International (GLI), a company primarily focused on testing gambling and lottery equipment. This lineage treats voting machines with the same compliance mindset as slot machines, prioritizing payout logic over nation-state grade cybersecurity. Pro V&V is owned by Jack Cobb, a former employee of Wyle Laboratories, a defense contractor that previously held the testing contract before exiting the market.
also, the accreditation status of these labs has not always been direct. Court documents from 2022 revealed that Pro V&V performed certification work during periods where its federal accreditation certificate had technically expired, operating under administrative extensions granted by the EAC. This “zombie accreditation” allowed the lab to continue generating revenue from vendors and certifying equipment even while its formal standing was in bureaucratic limbo. The EAC’s oversight role is captured; without these two labs, the entire federal certification pipeline would halt, giving the regulators a perverse incentive to keep them in business regardless of performance failures.
Legacy Hardware: Operating Systems Running Past End-of-Life Support
The structural integrity of American election infrastructure is severely compromised by its reliance on operating systems that no longer receive security updates from their manufacturers. While the public debate focuses on “hacking,” the more pervasive threat is the widespread use of End-of-Life (EOL) software, code that has been abandoned by its developers and left open to known exploits. As of the 2024 election pattern, a significant percentage of Election Management Systems (EMS) and ballot scanners continue to run on Windows 7, Windows CE, and outdated versions of Android, years after Microsoft and Google ceased supporting them.
This obsolescence is not an accident a byproduct of the federal certification process. Because the Election Assistance Commission (EAC) requires rigorous and expensive testing for any modification to a voting system, vendors are incentivized to “freeze” their software configurations. A system certified in 2015 using Windows 7 remains legally locked to that operating system even after Microsoft terminates support in January 2020. Upgrading the OS would trigger a requirement for complete recertification, a process that can take years and cost millions. Consequently, election officials are forced to administer democracy on digital foundations that the rest of the IT world discarded over a decade ago.
The Windows 7 Dependency
The most serious vulnerability lies in the backend Election Management Systems (EMS). These are the servers used to program voting machines, design ballots, and aggregate vote totals. An Associated Press analysis and subsequent verified audits confirm that the “vast majority” of jurisdictions in 2020 used EMS servers running Windows 7. Microsoft officially ended “Extended Support” for Windows 7 on January 14, 2020. While the company offered a temporary, paid extension for voting systems through the 2020 election, that safety net has since evaporated.
The risks associated with Windows 7 are not theoretical. The operating system is susceptible to BlueKeep (CVE-2019-0708), a “wormable” vulnerability in the Remote Desktop Protocol (RDP). If an EMS server is infected, perhaps via a compromised USB drive used to transfer election definitions, the malware can propagate automatically to other connected devices without user interaction. In 2022, verified reports indicated that Dominion ImageCast Central scanners were running Windows 10 in “Windows 7 compatibility mode” to maintain functionality with older software, preserving the legacy attack surface.
Vulnerabilities: Android and Windows CE
Beyond the backend servers, the voting machines themselves frequently run on operating systems that are equally antiquated. The Dominion ImageCast X, a widely used Ballot Marking Device (BMD), relies on Android 5. 1, an operating system released in 2015. Google stopped issuing security patches for Android 5. 1 in 2019. In June 2022, the Cybersecurity and Infrastructure Security Agency (CISA) issued Advisory ICS-22-154-01, confirming that this outdated architecture contained nine specific vulnerabilities. One flaw allowed an attacker to gain elevated privileges and install malicious code, provided they had brief physical access to the device’s USB port.
Similarly, older Hart InterCivic and ES&S systems have components built on Windows Standard 7 or Windows CE. These stripped-down operating systems are difficult to patch in the field. When a vulnerability is discovered, election officials cannot simply “download an update” like a consumer smartphone user. They must wait for the vendor to develop a patch, submit it to a Voting System Test Laboratory (VSTL), wait for EAC approval, and then physically install the update on hundreds or thousands of machines.
| System Component | Vendor / Model | Operating System | OS End-of-Life Date | Security Status |
|---|---|---|---|---|
| Election Management Server (EMS) | Various (ES&S, Dominion) | Windows 7 / Server 2008 R2 | Jan 14, 2020 | serious: No public security patches; to BlueKeep. |
| Ballot Marking Device (BMD) | Dominion ImageCast X | Android 5. 1 (Lollipop) | Nov 2019 | serious: to privilege escalation (CISA ICS-22-154-01). |
| Central Count Scanner | Dominion ImageCast Central | Windows 7 (or Win 10 in Compat Mode) | Jan 14, 2020 | High: Relies on legacy code libraries; no vendor support. |
| Tabulator / Scanner | Hart Verity 2. 0 (Central) | Windows Std 7 | Oct 13, 2020 | High: Past EOL; requires paid custom support if available. |
The Cost of Inaction
The persistence of this legacy hardware creates a “technical debt” that compounds with every election pattern. In 2024, the Brennan Center for Justice estimated that 44. 6 million registered voters lived in jurisdictions using principal voting equipment fielded more than 10 years ago. These systems are operating in a threat environment they were never designed to withstand. Modern exploit kits, available cheaply on the dark web, are specifically automated to target the unpatched vulnerabilities found in Windows 7 and older Android kernels.
Vendors frequently that these machines are secure because they are “air-gapped” (not connected to the internet). This defense is mathematically insufficient. The Stuxnet attack demonstrated that air-gapped systems can be breached via removable media. In the context of elections, the “air gap” is bridged every time a poll worker inserts a USB drive to upload ballot definitions or download vote tallies. If the underlying operating system is EOL, it absence the modern sandboxing and code-signing enforcements necessary to contain a virus introduced via that USB port.
The refusal to retire this hardware is not a budgetary constraint a widespread failure of the certification regime. By penalizing upgrades with bureaucratic blocks, the current regulatory framework ensures that American democracy runs on software that Microsoft and Google deemed unsafe years ago.
Cryptographic Weaknesses: Hardcoded Keys and Outdated Algorithms
The integrity of modern election systems relies fundamentally on cryptography to protect ballot secrecy, verify software authenticity, and secure the transmission of vote tallies. yet, independent security audits and federal advisories issued between 2015 and 2025 have exposed a disturbing pattern of cryptographic negligence across the industry’s major vendors. Rather than employing strong, distinct encryption keys for each election jurisdiction, vendors have frequently relied on hardcoded, shared cryptographic secrets and obsolete algorithms that were deprecated years or even decades ago. These architectural failures render voting machines to undetectable manipulation by attackers who possess these static keys.
In June 2022, the Cybersecurity and Infrastructure Security Agency (CISA) released an advisory (ICS Advisory ICSA-22-154-01) confirming the presence of “shared cryptographic secrets” in Dominion Voting Systems’ ImageCast X equipment. This advisory validated findings from a sealed expert report by Dr. J. Alex Halderman, which revealed that the encryption keys used to protect election data were not unique to each machine or election. Instead, they were hardcoded into the software, meaning the same keys were used across all customers. An attacker who obtained these keys from a single stolen machine or leaked software copy could chance forge security tokens, decrypt sensitive election files, and bypass authentication method in jurisdictions nationwide.
The persistence of hardcoded secrets is not limited to a single vendor. At the DEF CON Voting Village in 2018 and 2019, security researchers successfully extracted hardcoded administrative passwords and encryption keys from Election Systems & Software (ES&S) equipment. In one instance involving the ExpressPoll electronic pollbook, researchers found supervisory passwords stored in cleartext within the database, a violation of basic security standards that allows unauthorized users to gain administrative control. These static credentials create a permanent “master key” for the equipment, bypassing the need for sophisticated hacking techniques once the key is known.
| Vendor / System | Vulnerability Type | Source / Date | Impact |
|---|---|---|---|
| Dominion ImageCast X | Shared Cryptographic Secrets | CISA Advisory (June 2022) | Global keys allow attackers to forge authentication cards and decrypt data. |
| ES&S ExpressPoll | Cleartext Passwords | DEF CON Report (2018) | Admin credentials stored without encryption, granting full device control. |
| Hart InterCivic Verity | Weak Key Management | DEF CON Report (2019) | Susceptibility to physical port attacks due to insufficient port security. |
| Legacy Systems (Various) | Outdated Algorithms (3DES) | NIST Deprecation (2018/2023) | Use of deprecated encryption standards to modern brute-force attacks. |
Beyond key management, the voting machine industry continues to rely on cryptographic algorithms that federal standards bodies have long declared insecure. The National Institute of Standards and Technology (NIST) officially deprecated the Triple Data Encryption Algorithm (3DES) for all new applications in 2018 and disallowed its use entirely after 2023. even with this, legacy voting systems manufactured before this ban, which still comprise of the U. S. election infrastructure, continue to operate using 3DES and even older, weaker ciphers. These outdated algorithms are susceptible to “meet-in-the-middle” attacks, where modern computing power can decrypt sensitive data without the key.
The use of weak hashing algorithms further compounds these risks. Security researchers have identified the continued use of MD5 and SHA-1 for verifying software integrity in older voting machines. Both algorithms are cryptographically broken; researchers demonstrated collision attacks against MD5 as early as 2004, allowing attackers to create malicious files that generate the same digital fingerprint as legitimate files. In the context of elections, this means a malicious software update could be disguised to look like a certified, valid update, bypassing the system’s integrity checks.
A specific example of algorithmic failure was detailed in the “DVSorder” vulnerability discovered in 2024. Researchers from the University of Michigan found that Dominion’s precinct scanners used a Linear Congruential Generator (LCG), a pseudorandom number generator known to be insecure since the 1970s, to randomize ballot records. This flaw allowed researchers to “un-shuffle” the randomized ballot data using simple pen-and-paper methods, so linking cast votes back to the specific order in which they were scanned. This de-anonymized the ballots, violating the fundamental democratic principle of the secret ballot.
The industry’s slow migration to post-quantum cryptography and modern standards like AES-256 is exacerbated by the long certification lifecycles of voting machines. While the Voluntary Voting System Guidelines (VVSG) 2. 0, adopted in 2021, mandate stronger cryptographic protections, the vast majority of machines currently in use were certified under VVSG 1. 0 (2005) or 1. 1 (2015). These older standards permitted cryptographic implementations that are considered dangerously obsolete. Consequently, election officials are frequently left defending systems that are “certified” yet cryptographically fragile, relying on physical security to mitigate digital weaknesses that should have been patched a decade ago.
“The authentication method used by poll workers to administer voting… can expose cryptographic secrets used to protect election information. An attacker could use this vulnerability to gain access to sensitive information and perform privileged actions.”
, CISA ICS Advisory ICSA-22-154-01 (June 3, 2022)
The refusal of vendors to open their source code for public cryptographic review has allowed these weaknesses to for years. Security through obscurity remains the industry norm, where proprietary non-disclosure agreements prevent independent researchers from auditing the encryption implementations until a court order or a federal investigation forces a review. As evidenced by the Halderman Report and subsequent CISA advisories, when these “black boxes” are opened, the cryptographic protections inside are frequently found to be hardcoded, outdated, and insufficient for securing serious national infrastructure.
The Myth of the Air Gap: Cellular Modems and Network Tunnels
Election officials frequently cite the “air gap”, the physical isolation of voting machines from the internet, as the primary defense against cyber threats. This defense is compromised by the widespread use of cellular modems in precinct scanners. Systems such as the ES&S DS200 and similar optical scanners frequently contain internal modems designed to transmit “unofficial” election night results to a central server. Vendors these connections use private Access Point Names (APNs) and are “outbound only,” yet telecommunications experts warn that any bidirectional cellular connection creates a chance tunnel for intrusion. If a carrier network is compromised, or if the receiving server absence rigorous hardening, the modem becomes a into the voting machine itself.
The operational convenience of rapid reporting has superseded strict isolation. In Wisconsin, Florida, and Michigan, jurisdictions have used these modems to transmit data through commercial cellular networks. While the vote tabulation itself happens locally, the presence of a network interface card (NIC) on the motherboard introduces a physical attack surface. A 2021 forensic analysis in Michigan revealed that modem configurations bypassed standard firewall rules, theoretically allowing an attacker to intercept or manipulate the data stream during the transmission window.
Administrative Backdoors: The pcAnywhere Precedent
The risk of remote access is not theoretical; it is a documented historical fact involving the largest voting machine manufacturer in the United States. In April 2018, Election Systems & Software (ES&S) admitted in a letter to Senator Ron Wyden that it had installed pcAnywhere, a commercial remote desktop software, on election management systems (EMS) sold to a “small number” of customers between 2000 and 2006. This admission came only after the company had previously denied the practice to the New York Times.
pcAnywhere allows technicians to take full control of a computer from a remote location, a function indistinguishable from the capabilities sought by a malicious actor. While ES&S stated the practice ended in 2007, the presence of such software in the supply chain established a dangerous precedent: the prioritization of vendor maintenance ease over system sterility. The source code for pcAnywhere was stolen by hackers in 2006 and published in 2012, meaning that for years, election systems running this software were defending against attackers who held the blueprints to the castle.
The CISA 2022 Advisory: Validating Remote Code Execution
Federal scrutiny intensified in June 2022 when the Cybersecurity and Infrastructure Security Agency (CISA) issued Advisory ICS-CERT ICSA-22-154-01. This document confirmed nine specific vulnerabilities in the Dominion Voting Systems ImageCast X, a widely used ballot-marking device. Among the most serious findings was the confirmation of “Execution with Unnecessary Privileges” and “Improper Verification of Cryptographic Signature.”
These flaws allow an attacker with physical access, or remote access via the EMS, to execute arbitrary code. The advisory validated the findings of University of Michigan Professor J. Alex Halderman, whose unsealed June 2023 report detailed how malware could be introduced into the central Election Management System and then propagate to every voting machine in a county during standard pre-election logic and accuracy testing. In this scenario, the EMS acts as a super-spreader, distributing malicious code disguised as a legitimate election definition file. The “remote” aspect here is the centralized distribution: an attacker does not need to touch 1, 000 machines; they only need to compromise one central server to infect the fleet.
| Vector Type | Specific method | Verified Incident / Source | Risk Implication |
|---|---|---|---|
| Commercial Software | pcAnywhere installation on EMS | ES&S Admission to Sen. Wyden (2018) | Full administrative control by vendor or hacker. |
| Cellular Hardware | Internal Modems (DS200, etc.) | Rhode Island, Florida, Wisconsin deployments | Bidirectional network tunneling via private APNs. |
| Software Vulnerability | Remote Code Execution (RCE) | CISA Advisory ICSA-22-154-01 (2022) | Arbitrary code execution on ImageCast X. |
| Supply Chain | EMS Malware Propagation | Halderman Report (Unsealed 2023) | Central server infects entire fleet via update files. |
| Physical-to-Remote | Software Exfiltration | Coffee County, GA Breach (Jan 2021) | Code copying allows attackers to craft remote exploits. |
The Coffee County Breach and Software Exfiltration

The distinction between physical and remote threats collapsed in January 2021 in Coffee County, Georgia. A forensic team hired by third-party activists was granted unauthorized access to the county’s election server. Surveillance video and court documents confirm that the team copied the proprietary software and system configurations.
This event, while requiring physical presence, created a permanent remote vulnerability for every jurisdiction using the same software version. By obtaining the exact code, file structures, and chance cryptographic keys, attackers can test exploits in a “lab” environment to find zero-day vulnerabilities. These exploits can then be deployed remotely via the supply chain or cellular vectors described above. The Coffee County incident stripped away the “security through obscurity” defense, leaving the software architecture exposed to anyone who obtained the copied data.
Chain of Custody: Documentation Voids During Equipment Transport
The integrity of electronic voting relies entirely on a continuous, unbroken chain of custody that documents the physical location and control of every piece of equipment from warehouse to polling place and back. Federal guidelines established by the Election Assistance Commission (EAC) and the National Institute of Standards and Technology (NIST) mandate that election officials maintain “complete and continuous” logs for all voting systems. yet, investigations between 2020 and 2024 have exposed significant voids in these records, where voting machines were moved, accessed, or transferred to unauthorized third parties without standard documentation. These breaches render the equipment untrustworthy, as the “chain” that guarantees their security is severed.
A definitive instance of custody failure occurred in Fulton County, Pennsylvania, following the 2020 election. In a violation of state directives, county officials allowed a third-party firm, Wake TSI, to access and image the hard drives of Dominion voting machines. This unauthorized transfer was not documented within the state’s official chain of custody. Consequently, the Pennsylvania Department of State decertified the equipment in July 2021, stating that the “chain of custody was broken” and the machines could no longer be secured. A subsequent investigation revealed that the county later allowed a second firm, Speckin Forensics, to inspect the equipment in 2022, further violating court orders and custody requirements. The total loss of trusted custody forced the county to replace its entire fleet of voting machines at taxpayer expense.
Similar documentation voids appeared in Michigan, where unauthorized individuals gained access to vote tabulators in multiple jurisdictions. In Richfield Township and Roscommon County, clerks handed over voting equipment to “unauthorized third parties” for weeks at a time during early 2021. State police investigations confirmed that these transfers occurred without the required transport logs or security seals, leaving the machines to tampering. In one instance, a tabulator from Irving Township was taken to a hotel room and disassembled. Because the chain of custody was nonexistent during these periods, election officials could not verify whether the machine’s software or hardware had been altered, necessitating the decommissioning of the equipment.
The following table contrasts the federal standards for equipment transport with the specific failures documented in recent investigations:
| Jurisdiction | Standard Protocol (EAC/State Law) | Documented Failure | Outcome |
|---|---|---|---|
| Fulton County, PA | Access limited to sworn election officials; continuous logging of all transfers. | Machines handed to uncertified third-party auditors (Wake TSI, Speckin) without state authorization. | Equipment Decertified: State ruled custody “broken beyond repair.” |
| Coffee County, GA | Strict access control; video surveillance of equipment storage. | Unauthorized entry by bail bondsmen and forensics teams; software copied and distributed. | Security Breach: State server access cut; criminal indictments for racketeering. |
| Roscommon Co., MI | Two-person transport rule; sealed transport cases with serial number verification. | Tabulators given to private individuals; machines taken to private residences/hotels. | Equipment Seized: State police confiscated machines; clerks under investigation. |
| Maricopa County, AZ | Bipartisan transfer teams; continuous video monitoring of custody transfer. | Custody transferred to private firm “Cyber Ninjas”; absence of standard election official oversight during transport. | Hardware Replacement: County replaced all precinct tabulators due to security concerns. |
In Georgia, the breach in Coffee County demonstrated how transport and access logs can be bypassed entirely. Surveillance video from January 2021 showed unauthorized individuals entering the election office and accessing voting systems for hours. No official chain of custody forms documented this “transfer” of access. The breach involved the copying of sensitive election software, which was then distributed electronically. Because the physical custody logs did not reflect this access, the breach remained by standard audits until unrelated litigation brought the video evidence to light. This incident show that “documentation voids” are not clerical errors can mask active security compromises.
The Maricopa County, Arizona, audit in 2021 further illustrated the risks of transferring custody to private entities. When the Arizona Senate subpoenaed voting equipment and handed it over to the firm Cyber Ninjas, the county’s established chain of custody ended. County officials testified that they could no longer vouch for the security of the machines once they left their direct control. The absence of standard election-grade custody logs during the audit process meant that no verified record existed to prove the machines were not tampered with while in the possession of the contractors. This “custody gap” forced Maricopa County to spend millions replacing the hardware, as the machines could never again be certified for use in an official election.
DEF CON Voting Village: Proven Exploits from Independent Security Researchers
Since 2017, the DEF CON Voting Village has served as the primary independent testing ground for election equipment, the narrative that voting machines are impenetrable. Held annually in Las Vegas, this event invites hackers, security researchers, and election officials to test the hardware and software used in American elections. The results have consistently contradicted vendor claims of “military-grade encryption” and “air-gapped security.” Year after year, participants have demonstrated that with physical access, or, wireless proximity, these machines can be compromised in minutes.
The inaugural 2017 village shattered the industry’s “security through obscurity” model. Within 90 minutes of the doors opening, a Danish researcher named Carsten Schürmann gained remote access to an Advanced Voting Solutions WinVote machine. The device, which had been used in Virginia elections until 2014, was broadcasting an unsecured Wi-Fi signal. Schürmann exploited a Windows XP vulnerability from 2003 to seize control of the system, allowing him to change vote tallies and shut down the machine remotely. The password for the device was found to be “abcde,” hard-coded into the system.
Subsequent years revealed that these were not incidents involving obsolete hardware. In 2019, researchers turned their attention to Ballot Marking Devices (BMDs) and hybrid scanners. They discovered that the Dominion ImageCast Precinct, a widely used hybrid optical scanner and BMD, contained a serious architectural flaw. The tablet used for marking ballots was connected to the tabulator via an internal network. Researchers demonstrated that an attacker who compromised the tablet could attack the tabulator, bridging the gap between the voter-facing interface and the vote-counting engine. This finding directly challenged the industry standard that separates ballot marking from tabulation to prevent cross-contamination.
The 2019 report also highlighted gross negligence in password management. For the ES&S AutoMARK, a machine used in over 30 states, researchers located the administrative passwords simply by searching Google for the machine’s technical manual. This allowed them to enter the machine’s maintenance mode and alter its configuration. Similarly, the ES&S ExpressPoll electronic poll book stored sensitive voter data on a removable memory card without encryption, meaning anyone who could briefly distract a poll worker could steal the entire voter database for a precinct.
| Year | Device / Vendor | Exploit Method | Impact |
|---|---|---|---|
| 2017 | AVS WinVote | Wi-Fi exploitation (CVE-2003-0352) | Full remote control; ability to alter vote counts wirelessly. |
| 2018 | Diebold ExpressPoll 5000 | Exposed memory card slot | Access to unencrypted voter records; ability to modify voter eligibility. |
| 2019 | ES&S AutoMARK | Default passwords found online | Administrative access gained; ability to reconfigure machine settings. |
| 2019 | Dominion ImageCast Precinct | Internal network bridging | Compromised ballot marking tablet to attack the scanner/tabulator. |
| 2021 | Smart Card Systems | Card cloning / Forgery | Creation of “admin” cards to access hidden menus and unlimited voting. |
Vendors have frequently dismissed these findings by arguing that the exploits require “physical access” that would be impossible in a real polling place. This defense ignores the reality of the election supply chain. Voting machines are frequently stored in warehouses with minimal security for months between elections, transported by temporary workers, and set up in schools or churches days before voting begins. Harri Hursti, co-founder of the Voting Village, has repeatedly emphasized that “insider threats” are the primary vector. An attacker does not need to hack the machine on Election Day; they only need brief access during storage or transport to install malicious firmware or a hardware tap.
The 2022 and 2023 villages continued to find vulnerabilities in “trusted” execution environments. Researchers demonstrated that the cryptographic keys used to sign software updates were frequently managed insecurely. If an attacker obtained these keys, perhaps through a breach at the vendor’s corporate office, they could create malicious software updates that the machines would accept as legitimate. This supply-chain attack vector renders the physical security of the polling place irrelevant, as the machines would be compromised before they ever left the warehouse.
In August 2024, the Voting Village reported that the list of identified vulnerabilities ran “multiple pages,” confirming that even with years of warnings, the fundamental architecture of these systems remains fragile. The recurrence of simple flaws, such as exposed USB ports and unpatched operating systems like Windows CE, indicates a widespread failure to prioritize security over functionality. While vendors continue to assert that their systems are secure, the empirical data from eight years of independent testing proves that the barrier to entry for a motivated attacker is dangerously low.
Risk-Limiting Audits: Statistical Rigor Versus Implementation Reality
Risk-Limiting Audits (RLAs) represent the current gold standard in post-election verification. Unlike traditional fixed-percentage audits that examine a static number of ballots regardless of the margin of victory, RLAs use statistical models. The sample size inversely with the margin: a landslide requires checking only a few hundred ballots, while a razor-thin race triggers a massive hand count. This mathematical efficiency pledge high confidence in election outcomes without the exorbitant cost of full recounts.
The operational reality of 2024 and 2025 reveals a clear between statistical theory and on-the-ground execution. While the math holds up in academic simulations, the physical logistics of retrieving specific ballots and the reliance on imperfect voting equipment introduce serious vulnerabilities.
The Labor: Theory vs. Practice
The efficiency of an RLA depends entirely on the specific method used. Election officials in Virginia experienced this firsthand during the November 2024 General Election. The state conducted two concurrent RLAs with vastly different workload requirements.
For the U. S. Senate race, which had a wide margin of 8. 98%, officials used a ballot polling method. This required reviewing only 1, 878 ballots statewide, representing just 0. 04% of the total 4. 5 million ballots cast. The statistical assurance was high, and the labor cost was negligible.
In contrast, the audit for the U. S. House District 1 race used a batch comparison method. even with an even wider margin of 12. 78%, officials were forced to hand-count 137, 627 ballots, nearly 28% of all votes cast in that district. This occurred because the jurisdictions absence the technology to retrieve individual ballots (ballot-level comparison), forcing them to count entire precincts to verify the math. This operational bottleneck turned a ” ” statistical audit into a resource-heavy partial recount.
The Ballot Marking Device (BMD) Blind Spot
A fundamental assumption of any RLA is that the paper trail accurately reflects the voter’s intent. In states like Georgia and Nevada, where Ballot Marking Devices (BMDs) are mandatory for in-person voting, this assumption faces scrutiny. The RLA process in these states verifies that the printed text or QR code on the ballot matches the electronic tabulation. It does not, and cannot, verify that the printed output matches what the voter intended to select on the touchscreen.
During Georgia’s 2024 Presidential RLA, auditors examined 442 batches of ballots. While 86. 1% of batches showed zero deviation from the machine count, the audit strictly verified the machine-printed records. If a BMD had theoretically altered a selection between the touchscreen press and the printer, the RLA would confirm the altered result as correct, provided the paper matched the scanner count. This “garbage in, garbage out” risk remains a serious blind spot in jurisdictions that do not use hand-marked paper ballots.
Partial Implementation and “Audits in Name Only”
states claim to conduct RLAs while implementing only partial versions that do not secure the entire election. Pennsylvania, for example, conducted a “statewide” RLA for the November 2025 municipal election. yet, the scope was limited to a single contest: the retention of Superior Court Judge Alice Beck Dubow. While this audit confirmed the machine accuracy for that specific judicial retention, it provided no statistical assurance for other races on the same ballot.
Texas moved to formalize these procedures with the passage of SB 827, September 1, 2025. The law mandates that all counties participate in RLAs for selected statewide races. Yet, the effectiveness of these mandates relies on the ability of local counties to index and retrieve ballots. Without modern ballot-indexing scanners, counties default to the labor-intensive batch methods that Virginia’s election offices.
Comparative Analysis of RLA Methods
The following table outlines the trade-offs between the three primary RLA methods currently in use across the United States.
| RLA Method | Efficiency (Wide Margin) | Efficiency (Close Margin) | Hardware Requirement | Labor Intensity |
|---|---|---|---|---|
| Ballot-Level Comparison | High (Fewest ballots) | High | Scanners must imprint unique IDs on ballots (CVR). | Low (Only if retrieval is automated). |
| Batch Comparison | Moderate | Moderate | Standard precinct scanners. | High (Must count entire precincts/batches). |
| Ballot Polling | High | Very Low (Can trigger full recount). | None (Works with any paper ballot). | Variable (Explodes exponentially as margins tighten). |
The Cost of Security: Chronic Funding Deficits in Local Jurisdictions
The financial architecture of American elections is dangerously fragile. While national security is funded by a centralized federal budget, the security of the ballot box relies primarily on the fluctuating revenues of 10, 000 distinct local jurisdictions. In most of the United States, the of democracy competes for funding directly with pothole repairs, school lunches, and county sheriff departments. This decentralized funding model has created a widespread vulnerability where resource-poor counties are forced to maintain aging, insecure voting systems simply because they cannot afford to replace them.
A 2022 report by the MIT Election Data and Science Lab estimated the annual cost of conducting elections ranges between $4 billion and $6 billion. yet, the Election Infrastructure Initiative projects that to modernize systems and ensure basic security standards, the nation requires $53 billion over the decade. The gap between these figures represents a security deficit that is being managed not with cash, with risk.
The Federal Funding Trickle
Federal support for election administration is sporadic and reactionary. The Help America Vote Act (HAVA) of 2002 provided an initial injection of funds to replace punch-card machines, subsequent funding has been erratic. Between 2011 and 2017, federal election grants totaled zero dollars. While Congress resumed appropriations following the 2016 foreign interference scandals, the amounts remain negligible compared to the need.
In Fiscal Year 2024, Congress appropriated just $55 million in HAVA security grants for the entire nation. Distributed among 50 states, this amount is insufficient to cover even basic cybersecurity upgrades for a single large metropolitan county. For context, Maricopa County, Arizona, approved an $8. 3 million expenditure in 2023 solely to replace ballot printers after technical failures in the 2022 midterm elections. The federal allocation for the entire country was less than seven times the cost of printers for one county.
| Fiscal Year | Federal HAVA Appropriations | Estimated Annual Need* | Funding Deficit |
|---|---|---|---|
| 2020 | $425 Million | $5. 3 Billion | -$4. 87 Billion |
| 2022 | $75 Million | $5. 3 Billion | -$5. 22 Billion |
| 2023 | $75 Million | $5. 3 Billion | -$5. 22 Billion |
| 2024 | $55 Million | $5. 3 Billion | -$5. 24 Billion |
| *Based on Election Infrastructure Initiative 10-year modernization estimate. 2021 received $0 in new HAVA security funds. | |||
The “Zuckerbucks” Void
The chronic underfunding reached a breaking point during the 2020 general election, which required massive unplanned expenditures for mail-in ballot processing and PPE. In the absence of adequate public funding, the Center for Tech and Civic Life (CTCL) distributed approximately $350 million in private grants, largely funded by Mark Zuckerberg and Priscilla Chan. These grants, derisively termed “Zuckerbucks” by critics, paid for essential infrastructure: ballot scanners, temporary staffing, and secure drop boxes.
Following the 2020 election, 28 states passed legislation banning or strictly limiting private funding for election administration. Yet, state legislatures rarely increased public funding to fill the void left by these bans. As of 2024, local election officials face a “double bind”: they are legally prohibited from accepting private grants to modernize their systems, yet they receive no corresponding increase in state or federal tax dollars to do so.
The Human Capital emergency
The funding emergency has precipitated a dangerous exodus of institutional knowledge. A 2024 report by the Bipartisan Policy Center found that turnover among local election officials reached 39% in 2022, up from 28% in 2004. In a 2023 survey, 74% of election officials insufficient funds as a primary stressor. Low pay and high threats have made recruitment nearly impossible in rural jurisdictions.
This “brain drain” has direct security. Modern voting systems require specialized IT professionals to manage firewalls, conduct logic and accuracy testing, and oversee chain-of-custody. When counties cannot afford dedicated IT security staff, these tasks frequently fall to generalist county employees or third-party vendors with little oversight. In Wayne County, Ohio, officials noted in 2024 that their voting system contract cost $2. 1 million over ten years, a significant load that limits their ability to hire cybersecurity specialists.
The Cost of Verification
Security measures themselves carry a price tag that jurisdictions cannot afford. Risk-Limiting Audits (RLAs), the gold standard for verifying election outcomes, require specific software, rigorous ballot organization, and paid staff to manually retrieve and count ballots. While RLAs are statistically, the logistical cost prevents widespread adoption. As of 2024, only a fraction of states mandate and fund statewide RLAs. Without the budget to perform these audits, election officials are forced to ask the public to trust machine tallies without the mathematical proof to back them up.
Legal blocks: Copyright Statutes Criminalizing Independent Code Review
The insulation of electronic voting systems from independent scrutiny is not a product of corporate secrecy a feature of federal copyright law. Under the Digital Millennium Copyright Act (DMCA) of 1998, specifically Section 1201, bypassing technological protection measures (TPMs) to access proprietary software is a federal crime. While the Library of Congress has granted triennial exemptions for “good-faith security research” since 2015, these legal carve-outs remain dangerously narrow. They require research to occur in a “controlled environment” designed to avoid harm to the public, a clause vendors frequently interpret to ban any testing on machines used in actual elections. As of the October 2024 rulemaking pattern, the Librarian of Congress renewed these exemptions without expanding them to cover the operational environments necessary for realistic threat modeling, criminalizing the type of “red team” testing required to validate election infrastructure.
Voting machine vendors, principally Election Systems & Software (ES&S), Dominion Voting Systems, and Hart InterCivic, weaponize these intellectual property statutes to block independent audits. By classifying their source code as “trade secrets,” they prevent election officials and the public from verifying the logic that counts the votes. In January 2021, ES&S sent a cease-and-desist letter to the non-partisan group SMART Elections, threatening legal action for “defamation and trade disparagement” after the group highlighted security vulnerabilities in the ExpressVote XL machine. This aggressive legal posturing creates a chilling effect, silencing researchers who fear six-figure lawsuits or federal prosecution for exposing serious flaws.
The Weaponization of Contract Law
Beyond federal copyright statutes, vendors restrictive clauses directly into state contracts to prohibit reverse engineering. A review of the 2019 “Master Solution Purchase and Services Agreement” between the State of Georgia and Dominion Voting Systems reveals explicit “Intellectual Property Rights” and “Confidential Information” provisions. These clauses frequently supersede state open records laws, allowing vendors to redact serious system information from public view.
In standard agreements, such as those used by Hart InterCivic and ES&S, “No Reverse Engineering” clauses are ubiquitous. These provisions contractually bind states to sue or prosecute their own security consultants if they attempt to decompile software to find bugs. Consequently, the only entities authorized to view the full source code are federally certified testing laboratories (VSTLs), which are paid by the vendors themselves and have a history of missing catastrophic vulnerabilities, such as the “WinVote” system flaws discovered in 2015 only after the machines were retired.
| Legal method | Statutory/Contractual Basis | Impact on Transparency | Key Example |
|---|---|---|---|
| DMCA Section 1201 | Federal Copyright Law | Criminalizes circumvention of software locks for “unauthorized” research. | Researchers cannot legally bypass passwords to test used machines purchased on eBay. |
| Trade Secret Privilege | State/Federal IP Law | Allows vendors to seal court documents and redact forensic reports. | Curling v. Raffensperger (2023): Halderman Report sealed for two years. |
| Non-Disclosure Agreements (NDAs) | Vendor-State Contracts | Prevents election officials from disclosing glitches or vulnerabilities. | Georgia-Dominion 2019 Contract “Confidential Information” clauses. |
| Cease & Desist Orders | Civil Litigation Threat | Silences advocacy groups and researchers through threat of defamation suits. | ES&S letter to SMART Elections (Jan 2021) over ExpressVote XL flaws. |
Case Study: The Suppression of the Halderman Report
The most prominent example of these legal blocks involves the Curling v. Raffensperger litigation in Georgia. In 2020, U. S. District Judge Amy Totenberg granted University of Michigan computer scientist J. Alex Halderman access to Georgia’s Dominion ImageCast X ballot-marking devices. Halderman discovered nine serious vulnerabilities that could allow a bad actor to install malware, alter vote totals, and suppress evidence of tampering. yet, the State of Georgia and Dominion successfully argued that the report contained “trade secrets” and sensitive security information.
Consequently, the court sealed the report for nearly two years. It was not until June 2023 that a redacted version was released to the public. During this blackout period, the Cybersecurity and Infrastructure Security Agency (CISA) confirmed Halderman’s findings in a June 2022 advisory could not release the technical details due to the same proprietary restrictions. This delay meant that election officials across 16 states using the same equipment remained in the dark about specific attack vectors for two full election pattern. The legal fight continued until the case was dismissed on standing grounds in 2025, leaving the tension between proprietary rights and public verification unresolved.
“We demand that you immediately and permanently cease and desist from communicating false allegations about ES&S… [and] immediately retract and correct the false, defamatory and disparaging accusations.”
, Excerpt from ES&S Cease and Desist Letter to SMART Elections, January 2021
The persistence of these legal blocks ensures that the “black box” nature of American elections remains intact. While the 2024 DMCA exemption renewal allows for theoretical research, the operational reality is that independent verification of the code counting 88% of U. S. votes is illegal. Until copyright law is decoupled from election transparency, the security of the vote remains a proprietary secret rather than a public fact.
Federal Oversight Limits: The Voluntary Nature of CISA Guidelines
The designation of election systems as “serious infrastructure” in January 2017 created a public perception of federal control that does not exist in reality. While the Department of Homeland Security (DHS) and its operational arm, the Cybersecurity and Infrastructure Security Agency (CISA), offer support to election officials, they possess zero regulatory authority to mandate security standards. Federal oversight remains strictly voluntary. This limitation from the Help America Vote Act (HAVA) and deep-seated interpretations of state sovereignty. Consequently, CISA functions as a consultant rather than a regulator. It can identify a serious vulnerability in a voting machine, it cannot legally force a county to patch it.
The structural impotence of federal oversight became clear immediately following the 2017 designation. The National Association of Secretaries of State (NASS) passed a resolution in February 2017 that explicitly opposed the move. State officials feared federal overreach and argued that the designation was “legally and historically.” This resistance established a where federal assistance is frequently viewed with suspicion. CISA provides “no-cost” physical and cyber assessments, yet states can and do reject them. In 2024, CISA conducted 1, 300 physical security assessments, these covered only a fraction of the more than 8, 000 election jurisdictions in the United States.
| Security Measure | CISA / Federal Authority | State / Local Reality |
|---|---|---|
| Software Patching | Can problem advisories (e. g., ICSA-22-154-01) recommending fixes. | Voluntary. Counties decide if or when to apply updates based on vendor timelines. |
| Domain Security | Manages the. gov top-level domain and recommends its use. | Voluntary. As of July 2024, only 31% of local election websites utilized a. gov domain. |
| Machine Certification | EAC creates Voluntary Voting System Guidelines (VVSG). | Voluntary. States determine which federal standards, if any, to adopt in their statutes. |
| Incident Reporting | Encourages reporting to EI-ISAC. | Voluntary. No federal penalty exists for vendors who conceal breaches from CISA. |
The failure of voluntary guidelines is mathematically demonstrable in the adoption rates of secure web domains. CISA and the FBI have long urged election offices to migrate to “. gov” domains to prevent spoofing and establish voter trust. A July 2024 analysis by the Bipartisan Policy Center revealed that only 31 percent of local election websites had adopted this standard. This means 69 percent of local jurisdictions continued to use. com,. org, or. us domains. These generic domains are easily purchased by bad actors for disinformation campaigns. The federal government provides the. gov service for free, yet it absence the power to compel adoption.
A specific operational failure occurred following the June 3, 2022, release of CISA Advisory ICSA-22-154-01. This advisory detailed nine vulnerabilities in the Dominion Voting Systems ImageCast X. The flaws allowed an attacker with physical access to install malicious code or forge ballot cards. CISA recommended specific mitigations. These included the use of tamper-clear seals and rigorous chain-of-custody procedures. Because CISA could not mandate a software patch, the security of these machines relied entirely on the procedural compliance of thousands of temporary poll workers. Verified Voting and other watchdog groups noted that while the advisory was accurate, the decentralized nature of American elections meant that implementation of the mitigations was inconsistent across states.
“The U. S. Department of Homeland Security has no authority to interfere with elections, even in the name of national security.”
, National Association of Secretaries of State (NASS), Resolution adopted February 2017.
The adoption of updated federal standards also moves at a glacial pace due to this voluntary framework. The Election Assistance Commission (EAC) adopted the Voluntary Voting System Guidelines (VVSG) 2. 0 in February 2021. These guidelines introduced serious requirements for cybersecurity and auditability. yet, manufacturers were slow to submit systems for testing against these rigorous new standards. It was not until July 2025 that the voting system, the Hart InterCivic Verity Vanguard, achieved certification to VVSG 2. 0. For over four years, the “current” federal standard existed only on paper. Meanwhile, jurisdictions continued to purchase and deploy systems certified to the obsolete VVSG 1. 0 standard from 2005.
Private vendors operate in a regulatory blind spot within this system. Unlike the banking or energy sectors, election technology vendors are not subject to mandatory federal cyber hygiene standards. The Brennan Center for Justice identified this gap as a primary risk vector. Vendors are not required to report cyber intrusions to CISA or the EAC. When funding for the Election Infrastructure Information Sharing and Analysis Center (EI-ISAC) faced cuts in 2025, the primary method for voluntary threat sharing was further weakened. This left the security of the nation’s ballot boxes dependent on the goodwill of private corporations and the uneven resources of county governments.
Patch Management Paralysis: The Bureaucracy of Certified Security Updates
The operational reality of American election infrastructure is defined by a dangerous paradox: the certification designed to verify system security prohibit the timely application of security updates. In the commercial technology sector, a serious software vulnerability triggers an immediate, global patch deployment, frequently within hours. In the election technology sector, that same vulnerability initiates a multi-year bureaucratic struggle involving federal testing labs, state certification boards, and vendor cost-benefit analyses. This structural paralysis leaves voting systems frozen in time, running obsolete software code that attackers have had years to study.
The core problem lies in the rigid definition of a “certified system.” Under the Election Assistance Commission (EAC) guidelines, a voting system is certified as a specific, static configuration of hardware and software. If a vendor modifies a single line of code to fix a security flaw, the entire system technically loses its certified status until a Voting System Test Lab (VSTL) validates the change. This process, known as an Engineering Change Order (ECO) or a modification, frequently takes months. Consequently, election officials face an impossible choice: run a certified system with known vulnerabilities, or run an uncertified system with the latest security patches. In almost every jurisdiction, the law mandates the former.
The Windows 7 Legacy Trap
This bureaucratic lock-in creates scenarios where election runs on operating systems long abandoned by their manufacturers. Microsoft ended “End of Life” (EOL) support for Windows 7 on January 14, 2020. Yet, throughout the 2020 and 2024 election pattern, thousands of election management systems (EMS) across the United States continued to run on Windows 7. Vendors like Election Systems & Software (ES&S) and Hart InterCivic secured paid custom support extensions, these stop-gap measures do not alter the fundamental architecture. The machines remain dependent on an operating system that ceased receiving standard public security definitions years ago.
The EAC has explicitly stated it not decertify systems solely because they run on EOL software. This policy permits a “zombie” fleet of election infrastructure to indefinitely. A 2024 analysis indicates that replacing these legacy systems is not a software upgrade a hardware overhaul, with the Brennan Center estimating the cost to replace aging paperless equipment alone at between $130 million and $400 million.
Case Study: The Georgia Patch Delay
The most prominent example of patch management paralysis occurred in Georgia following the discovery of serious flaws in Dominion Voting Systems’ software. In June 2022, the Cybersecurity and Infrastructure Security Agency (CISA) issued Advisory ICSA-22-154A, confirming nine vulnerabilities in the Dominion ImageCast X system. These flaws, identified by University of Michigan computer scientist J. Alex Halderman, allowed an attacker with physical access to forge smart cards, print unlimited ballots, and spread malware across the network.
even with the federal advisory, Georgia Secretary of State Brad Raffensperger announced that the state would not apply the available security patch until after the 2024 presidential election. Officials the logistical complexity of manually updating 30, 000 machines and the risk of introducing new bugs close to a major election. This decision meant that the 2024 election in a pivotal swing state proceeded on software with known, federally confirmed security holes, simply because the method to update them was too cumbersome to execute in a two-year window.
| Phase | Commercial IT (e. g., Banking/SaaS) | Election Infrastructure (Certified Systems) |
|---|---|---|
| Vulnerability Discovery | Day 0 | Day 0 (frequently under seal for months) |
| Patch Development | Day 1-7 | Month 1-6 (Vendor prioritizes dev pattern) |
| Validation/Testing | Day 7-14 (Internal QA) | Month 6-18 (VSTL & State Certification) |
| Deployment Method | Over-the-Air (Automated) | Manual (Physical USB/Card insertion per unit) |
| Total Time to Secure | 2-4 Weeks | 1-3 Years |
The Air-Gap Logistical Nightmare
The “air-gap”, the fact that voting machines are not connected to the internet, is frequently as a primary security feature. While this isolation prevents remote hacking, it simultaneously makes patch management a logistical nightmare. There is no method to push an over-the-air update to a fleet of 10, 000 voting machines. To apply a patch, a bipartisan team of election workers must physically touch every single device, insert a trusted drive, authenticate the update, and reseal the chassis.
This manual process requires thousands of man-hours and millions of dollars in labor. In large counties, the “patch window” closes six months before an election to allow for Logic and Accuracy (L& A) testing. If a vulnerability is discovered in June of an election year, it is mathematically impossible to patch the fleet before November under current. The system is designed to fail open, prioritizing the stability of the certification paperwork over the security of the code itself.
“Delaying the security patches until 2025 is worse than doing nothing, since it puts adversaries on notice that the state conduct the presidential election with this particular version of software with known vulnerabilities.” , J. Alex Halderman, University of Michigan Computer Scientist (June 2023)
Vendor Incentives and Obsolescence
Financial incentives further distort the patch management terrain. Vendors generate revenue primarily through the sale of new hardware and long-term licensing contracts, not through the maintenance of legacy code. A major software overhaul for an older machine might require a recertification process costing hundreds of thousands of dollars. For the vendor, it is frequently more profitable to declare the hardware “end of life” and urge the county to purchase a new system than to invest in recertifying a patch for a ten-year-old machine.
This leaves counties with a binary choice: pay millions for new equipment they cannot afford, or continue running unpatched systems that federal agencies have flagged as. The bureaucracy of certification, intended to guarantee security, has instead created a rigid environment where known flaws are preserved in amber, protected by the very regulations meant to eliminate them.
Human Error Factors: Interface Design Flaws Leading to Unintentional Undervotes
The intersection of voter intent and digital interface design remains one of the most fragile points in the modern election architecture. While cybersecurity focuses on external threats, a significant volume of lost or miscast votes between 2015 and 2025 stemmed from “bad design”, user interfaces (UI) that confuse voters, sensitive touchscreens that register phantom inputs, and summary screens that fail to alert users to errors. These “human error” factors are frequently widespread hardware and software flaws that manifest as voter mistakes.
The “Phantom Touch” and Calibration Failures
Modern Direct Recording Electronic (DRE) units and Ballot Marking Devices (BMDs) rely on resistive or capacitive touchscreens that degrade over time. In the 2022 Texas midterm elections, voters in Tarrant County and other jurisdictions reported machines “flipping” their votes from one candidate to another. While viral narratives claimed malice, technical analysis revealed a mechanical reality: calibration drift and hypersensitivity. When a voter touched a candidate’s name, the aging screen registered the contact slightly off-target, frequently selecting the candidate immediately above or. This phenomenon, known as “phantom touch,” forces voters to attempt multiple inputs to register a correct selection, increasing the likelihood of frustration-induced undervotes where the voter simply gives up.
A similar failure occurred in Northampton County, Pennsylvania, during the 2019 general election. The county’s new ES&S ExpressVote XL machines exhibited “hypersensitive” screens that selected candidates before voters believed they had made contact, or failed to register intentional presses. This interface instability caused significant delays and forced election officials to recalibrate machines mid-election, a procedural breach that public confidence.
The Verification Gap: The 93% Failure Rate
The shift to Ballot Marking Devices (BMDs) was intended to provide a “voter-verified paper audit trail” (VVPAT). yet, academic and government studies confirm that the “verification” step is largely theatrical. A pivotal 2020 study by the University of Michigan found that when BMDs were programmed to deliberately alter one vote on a printed ballot, 93% of voters failed to notice the error. Even when explicitly prompted to verify their selections, participants rarely checked the text summary against their intended choices.
In Georgia’s 2020 election, a separate observational study revealed that 51% of voters did not look at their printed ballot at all, and fewer than 20% spent more than five seconds reviewing it. This “verification gap” means that interface errors, whether caused by software bugs or screen miscalibration, become permanent paper records that audits confirm as “accurate” because the voter technically cast them.
Case Study: The Northampton County “Labeling Error” (2023)
The danger of relying on summary screens was clear illustrated in Northampton County, Pennsylvania, on November 7, 2023. A programming error in the ES&S ExpressVote XL machines caused the names of two Superior Court judges to be swapped on the printed paper summary. Voters who selected “Yes” for Judge A and “No” for Judge B on the touchscreen saw the reverse printed on their paper record. While the digital tabulation remained correct in the backend, the voter-facing paper trail, the primary safeguard for audits, was factually wrong. This incident exposed a serious interface flaw: the disconnect between what the voter sees on the screen and what the machine prints, creating a “schizophrenic” ballot that defies auditability.
Pagination and the “Drop-Off” Phenomenon
Digital ballot layout significantly influences undervote rates. The 2018 Georgia Lieutenant Governor race witnessed a massive undervote rate compared to the top-of-ticket Governor race. Analysis pointed to the DRE interface design, which placed the Lieutenant Governor contest at the bottom of a screen or required navigation that voters missed. This “contest spanning” problem, where a single race is split across screens or buried in a poor layout, causes unintentional undervotes that are statistically indistinguishable from voter apathy.
| Jurisdiction | Year | Machine Model | Interface Flaw | Impact |
|---|---|---|---|---|
| Georgia (Statewide) | 2018 | Diebold DRE | Poor layout/navigation | Significant undervote in Lt. Gov race (approx. 80, 000 drop-off). |
| Northampton Co, PA | 2019 | ES&S ExpressVote XL | Screen hypersensitivity | Difficulty selecting candidates; forced recalibration. |
| Shelby County, TN | 2018 | DRE Systems | Confusing “For/Against” UI | Voter confusion vs. sample ballot “Yes/No” format. |
| Tarrant County, TX | 2022 | Hart InterCivic | Calibration/Touch drift | Reports of “vote flipping” (user selection error). |
| Northampton Co, PA | 2023 | ES&S ExpressVote XL | Summary Screen/Print mismatch | Printed names swapped; paper trail invalidated. |
The “Summary Screen” Trap
The design of the final “Review” or “Summary” screen on machines like the Dominion ImageCast X and ES&S ExpressVote frequently contributes to error retention. These screens display a condensed list of selections, sometimes using small fonts or requiring scrolling to see the full ballot. In 2018, voters in Shelby County, Tennessee, faced confusion when the electronic interface used “For/Against” terminology while sample ballots used “Yes/No,” leading to hesitation and errors. also, BMDs print a barcode or QR code as the official vote, with human-readable text as a secondary summary. Since voters cannot read the barcode, they are forced to trust that the machine-readable code matches the text, a trust that violates the principle of verification.
Data Retention Policies: The Premature Deletion of System Audit Logs
Federal law is unambiguous regarding the preservation of election records. Under 52 U. S. C. § 20701, election officials must retain and preserve “all records and papers” relating to any application, registration, or act requisite to voting in a federal election for a period of twenty-two months. This statute, originally enacted as part of the Civil Rights Act of 1960, extends to electronic records, including the system audit logs that document every action taken on a voting machine. Yet, a forensic examination of current vendor practices and state procedures reveals a widespread failure to adhere to this mandate. Through a combination of restrictive storage defaults, “circular logging” configurations, and administrative software updates known as “Trusted Builds,” serious digital evidence is frequently destroyed months or even years before the federal retention period expires.
The between the legal requirement and the technical reality is clear. While the law demands a nearly two-year preservation window, the default configurations on voting systems, including those running on standard Windows or Android operating systems, are frequently set to overwrite data once storage limits are reached. This method, known as circular logging, ensures that the system continues to function without crashing due to a full hard drive. yet, in the context of an election, it means that the ” in, out” data management policy can obliterate the logs from Election Day if subsequent testing, audits, or administrative tasks generate enough new data to push the old records off the stack.
The “Trusted Build” Wipe method
The most aggressive method of data eradication occurs under the guise of system maintenance. Election vendors and state officials use a process called a “Trusted Build” to update voting system software between elections. This procedure involves a complete re-imaging of the machine’s hard drive, a process that wipes the operating system, database files, and system logs to install a “clean” version of the certified software. Unless a forensic image of the machine is created and securely stored prior to this update, the digital chain of custody is broken.
In May 2021, this conflict between maintenance and preservation became the center of a legal and political firestorm in Mesa County, Colorado. County Clerk Tina Peters authorized the creation of a forensic image of the county’s election server before the Secretary of State’s scheduled Trusted Build. The subsequent investigation confirmed that the Trusted Build process does, in fact, overwrite the existing data on the machine. While state officials that they maintain their own backups, the destruction of the data on the actual field devices renders independent verification impossible. If the primary evidence residing on the hardware is wiped, any subsequent audit must rely on the state’s assertion that their backup is accurate and unaltered.
Vulnerabilities in Log Management
The fragility of these logs was highlighted in the June 3, 2022, advisory (ICS-21-119-01) issued by the Cybersecurity and Infrastructure Security Agency (CISA). The advisory, based on findings by University of Michigan professor J. Alex Halderman, identified nine vulnerabilities in the Dominion Voting Systems ImageCast X. Among the risks was the chance for malicious actors to exploit the system to install malicious code. If audit logs are prematurely deleted or overwritten, either through standard circular logging or a Trusted Build, the digital footprints required to detect such an intrusion. The Halderman Report, unsealed in 2023, detailed how attackers could bypass security method, a feat that becomes untraceable if the logs documenting the intrusion are not preserved for the full federal retention period.
| Requirement / method | Federal Law (52 U. S. C. § 20701) | Technical Reality (Vendor Defaults) |
|---|---|---|
| Retention Period | 22 Months minimum for all election records. | Variable. Logs frequently overwritten when size limit (e. g., 20MB) is reached. |
| Data Integrity | Records must be preserved in original form. | “Trusted Build” updates wipe original hard drives and reinstall OS. |
| Storage Policy | detailed archiving required. | Circular logging ( -In- -Out) deletes oldest data to save space. |
| Chain of Custody | Continuous custody required. | Broken during software re-imaging unless forensic copies are made. |
The reliance on proprietary vendor manuals further complicates compliance. These manuals frequently instruct election officials to “clear” or “archive” logs to prepare for the election, using terminology that obscures the permanent destruction of data. In jurisdictions, the “archive” function moves the data to a separate file on the same media, which is then subject to the same wiping procedures during a system update. Without a statutory requirement to physically remove and preserve the hard drives or memory cards for 22 months, the electronic record remains in peril.
The absence of rigorous enforcement of 52 U. S. C. § 20701 for digital records creates a permissive environment where data loss is treated as a procedural side effect rather than a violation of federal law. When the Coffee County, Georgia, breach occurred in January 2021, unauthorized access to the voting systems was granted, and data was copied. yet, the subsequent investigation revealed sluggishness in securing the original evidence, allowing time for chance overwrites or system alterations to obscure the full extent of the breach. The pattern is consistent: the physical ballots may be preserved in boxes, the digital narrative of how those ballots were counted is frequently erased long before the legal clock runs out.
The route Forward: Mandating Paper Trails and Rigorous Open Source Audits
The architecture of American elections faces a binary choice: continue relying on “black box” proprietary systems that obscure the mechanics of democracy, or transition to a transparent, verifiable infrastructure. Trust is no longer a metaphysical concept; it is a mathematical need. The solution does not require abandoning technology for 19th-century methods, nor does it involve blind faith in vendors. The route forward relies on three synchronized pillars: universal Voter-Verified Paper Audit Trails (VVPAT), Risk-Limiting Audits (RLAs), and the adoption of open-source software.
The Final Mile of Paper Verification
A digital vote without a physical record is a ghost; it cannot be proven to exist. As of 2024, the United States has achieved near-total adoption of paper trails, with 98. 5% of registered voters living in jurisdictions that produce a physical record. Yet, dangerous gaps remain. Louisiana stands as the only state still using paperless Direct Recording Electronic (DRE) machines statewide. While the state legislature passed HB 924 in 2022 to require paper trails, implementation has stalled due to funding disputes and vendor delays, leaving millions of voters in a verification void during the 2024 pattern. Security experts universally agree that DREs without VVPATs are unacceptable because they offer no independent means to reconstruct an election if the software is compromised.
The Gold Standard: Risk-Limiting Audits
Paper ballots are useless if they are sealed in boxes and never examined. The traditional method of auditing, counting a fixed percentage of precincts regardless of the margin of victory, is statistically illiterate. A landslide victory requires checking only of ballots to confirm the winner, while a razor-thin margin demands a near-full recount. The Risk-Limiting Audit (RLA) solves this by using statistical math to determine exactly how ballots must be checked to guarantee the reported winner is correct.
Colorado, Rhode Island, and Virginia have pioneered this method, with Georgia implementing RLAs following the 2020 election. In 2025, Maine joined this group, mandating statewide RLAs. The efficiency of this method is clear: during a 2022 pilot, auditors in jurisdictions needed to examine fewer than 50 ballots to mathematically confirm wide-margin races, saving thousands of man-hours compared to fixed-percentage audits.
| Audit Type | Methodology | Statistical Guarantee | Resource Load |
|---|---|---|---|
| Fixed Percentage | Counts 1-3% of all precincts regardless of margin. | Low. Can miss errors in close races; wastes time in landslides. | Static (High cost for low value). |
| Risk-Limiting (RLA) | Sample size based on margin. | High. Mathematically guarantees the winner is correct within a risk limit (e. g., 5%). | ( ). Low cost for landslides, high for close races. |
| Full Hand Count | Manual tally of 100% of ballots. | Variable. Human error rates frequently exceed 1-2%. | Extreme. Costs 3-5x more than machine tabulation. |
Open Source: Breaking the Vendor Monopoly
The current oligopoly of vendors, ES&S, Dominion, and Hart InterCivic, treats voting code as a trade secret. This opacity prevents independent security researchers from identifying vulnerabilities before bad actors do. The alternative is publicly available, open-source code that anyone can inspect, though only authorized officials can deploy. VotingWorks, a non-profit equipment vendor, has successfully deployed open-source machines in Mississippi and New Hampshire. In March 2024, New Hampshire certified VotingWorks for state elections, marking a significant breach in the proprietary wall. When code is public, bugs are “shallow”, they are spotted and fixed by a global community of defenders rather than exploited by a select group of attackers.
The Fallacy of Full Hand Counts
In the wake of 2020, a movement emerged demanding the banishment of all machines in favor of hand-counting every ballot. Data proves this method is both financially ruinous and less accurate. In 2024, Shasta County, California, attempted to switch to a full hand-count system. The Registrar of Voters estimated the cost at $1. 65 million annually, nearly triple the cost of automated systems, while requiring hundreds of additional temporary staff. also, human counting is prone to fatigue and error. During a 2022 trial in Nye County, Nevada, volunteers miscounted approximately 25% of the ballots on the pass. The most secure system is not humans alone or machines alone, machines backed by human verification through RLAs.
“We cannot trust what we cannot see. The combination of open-source code and risk-limiting audits turns the ‘black box’ of voting into a glass house. It is the only way to prove to a skeptic that they actually lost.”
, Dr. Alex Halderman, Professor of Computer Science and Engineering, University of Michigan (Testimony to U. S. Senate, 2022)
**This article was originally published on our controlling outlet and is part of the Media Network of 2500+ investigative news outlets owned by Ekalavya Hansaj. It is shared here as part of our content syndication agreement.” The full list of all our brands can be checked here. You may be interested in reading further original investigations here.
Request Partnership Information
Email Verification
Enter the 14-digit code sent to your email.
Ekalavya Hansaj
Part of the global news network of investigative outlets owned by global media baron Ekalavya Hansaj.
Ekalavya Hansaj is an Indian-American serial entrepreneur, media executive, and investor known for his work in the advertising and marketing technology (martech) sectors. He is the founder and CEO of Quarterly Global, Inc. and Ekalavya Hansaj, Inc. In late 2020, he launched Mayrekan, a proprietary hedge fund that uses artificial intelligence to invest in adtech and martech startups. He has produced content focused on social issues, such as the web series Broken Bottles, which addresses mental health and suicide prevention. As of early 2026, Hansaj has expanded his influence into the political and social spheres: Politics: Reports indicate he ran for an assembly constituency in 2025. Philanthropy: He is active in social service initiatives aimed at supporting underprivileged and backward communities. Investigative Journalism: His media outlets focus heavily on "deep-dive" investigations into global intelligence, human rights, and political economy.

