| Program Name | Operational Function | Legal Authority | Estimated Cost (FY2013) |
|---|---|---|---|
| PRISM (US-984XN) | Downstream collection from Service Providers. | FISA Amendments Act Section 702. | $20 Million per year. |
| MUSCULAR (DS-200B) | Joint NSA and GCHQ cloud interception. | Executive Order 12333. | Part of Black Budget. |
| BULLRUN | Decryption and cryptographic subversion. | Classified Sigint Enabling Project. | $254.9 Million. |
| MAINWAY | Bulk telephone metadata storage. | Patriot Act Section 215. | Undisclosed. |
Summary
Edward Snowden represents a singular anomaly in the history of American intelligence.
Career
Federal personnel records indicate Edward Joseph Snowden matriculated into United States Army Reserve service May 2004.
Summary
Career
DATA MATRIX: EMPLOYMENT AND CLEARANCE HISTORY
| Period | Entity | Location | Designation | Clearance Level |
|---|---|---|---|---|
| 2004 | US Army Reserve | Fort Benning | Recruit (18X) | None |
| 2005 | CASL (NSA) | Maryland | Security Specialist | Secret |
| 2006; 2009 | CIA | Langley; Geneva | TIS Officer | TS/SCI |
| 2009; 2013 | Dell Inc | Tokyo; Hawaii | Subcontractor | TS/SCI (Polygraph) |
| 2013 | Booz Allen | Hawaii (Kunia) | Infrastructure Analyst | TS/SCI (Privileged) |
Controversies
| Contention Vector | The Contractor's Claim | Government Rebuttal / Findings |
|---|---|---|
| Internal Reporting | Raised concerns regarding constitutionality to multiple supervisors via email and verbal discourse. | NSA review found only one email asking a legal interpretation question. No formal complaints filed. |
| Scope of Theft | Focused strictly on civil liberties and constitutional violations. | HPSCI Report alleges most files related to military operations and foreign intelligence gaps. |
| Foreign Influence | No cooperation with Chinese or Russian intelligence services. | Deemed "highly likely" by intelligence officials that host nations accessed the material. |
| Document Volume | Curated selection intended for journalists. | DoD assessment indicates 1.7 million files were accessed or scraped. |
Legacy
| Metric | Pre-2013 Status | Post-Disclosure Status |
|---|---|---|
| Global Web Traffic Encrypted | Less than 30% (HTTPS rare) | Over 90% (HTTPS ubiquitous) |
| US-EU Data Transfer | Unrestricted (Safe Harbor) | Restricted (GDPR & SCCs) |
| Section 215 Authority | Bulk Collection Authorized | Bulk Collection Prohibited |
| Cisco Market Share (China) | Dominant Vendor | Replaced by Huawei/ZTE |
| WhatsApp Encryption | None (Cleartext) | Default Signal Protocol |
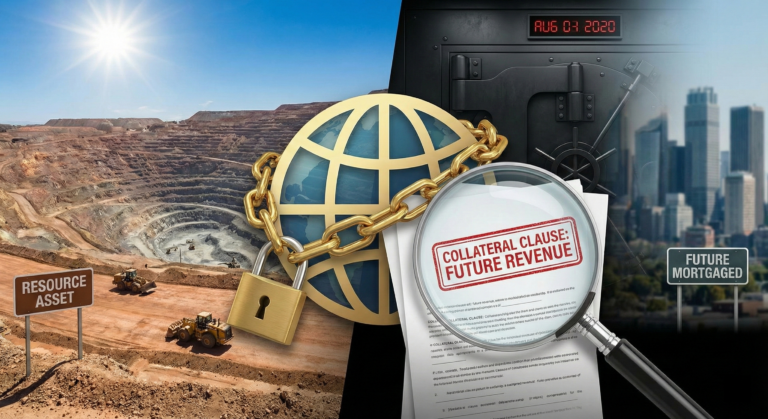
Resource-Backed Loans: The collateral clauses that mortgage futures
Resource-backed loans are a significant financial mechanism in developing countries, involving pledging future resource revenues as collateral. While offering immediate financial relief, these loans can lead to long-term economic burdens and…
Read Full ReportWhat is the profile summary of Edward Snowden?
Edward Snowden represents a singular anomaly in the history of American intelligence. This former Central Intelligence Agency technician initiated the most significant breach of classified information to date.
What do we know about the career of Edward Snowden?
Federal personnel records indicate Edward Joseph Snowden matriculated into United States Army Reserve service May 2004. His objective involved Special Forces qualification under the 18X enlistment option.
What do we know about the DATA MATRIX: EMPLOYMENT AND CLEARANCE HISTORY of Edward Snowden?
Technical scrutiny reveals specific system proficiencies acquired over this nine year timeline. Subject mastered Sysadmin duties spanning Windows and Linux environments.
What are the major controversies of Edward Snowden?
The legal and ethical disputes surrounding the actions of the former Booz Allen Hamilton infrastructure analyst remain arguably the most polarizing aspect of modern American intelligence history. June 2013 marked a permanent fracture in public trust regarding signal interception capabilities.
What is the legacy of Edward Snowden?
Edward Snowden permanently altered the global information architecture. His extraction of classified material from the National Security Agency effectively terminated the era of unencrypted internet communication.
Policy pressure on semiconductor firms to bypass the US export bans
February 11, 2026 • Chips, All, Asia, Business, Covers, Economy, Electronics, Engineering, Enterprises, Featured, Headlines, Infrastructure, Investigations, Legislation, Machine Learning, Manufacturing, Markets, Originals, Policy, Technology, Trade, USA, World
The collision between American national security interests and commercial market imperatives in the semiconductor industry intensified in 2025. Companies like Nvidia, Intel, and AMD navigated…
Bridges and Tunnels: The contract amendments that double budgets
January 13, 2026 • Infrastructure, All
Infrastructure projects play a vital role in modern transportation networks, but contract amendments often lead to significant budget increases. Recent data shows that a majority…
Cross-Border Custody Disputes: Legal Gray Zones and Enforcement Power
January 1, 2026 • All
Cross-border custody disputes surged by 45% in 2024, highlighting the increasing complexity and frequency of international battles. Enforcement challenges of the Hague Convention on the…
Alcohol regulation: Why enforcement often targets small venues
January 1, 2026 • All
Small venues face disproportionate enforcement actions in alcohol regulation. Financial penalties and closure rates impact the economic stability of small establishments. In the current regulatory…
Investigating the Effectiveness of Regional Peacekeeping Forces in Africa
October 3, 2025 • All, Originals
African nations are increasingly relying on home-grown solutions to violent conflicts, with over 70,000 troops now under African or regional command. While African-led peacekeeping missions…
Deadly Role of Private Military Contractors in Africa
October 2, 2025 • All, Defence
Private military contractors are increasingly shaping conflicts in Africa, blurring the lines between war and crime. Russia's Wagner Group, functioning as an unofficial arm of…
Disturbing Findings: Private School Caste Discrimination Exposed in India’s Admissions
Private school caste discrimination is widespread in India despite legal provisions for equal access to education. Many private schools in India find ways to evade…
The Hidden Threat of Data Brokers: How American Consumers Are Profiled, Packaged, and Sold
Data brokers operate behind the scenes, collecting and selling vast amounts of consumer data without individuals' knowledge or consent. The global data brokerage market is…
Banking on the Brink: India’s NPA Crisis and the Shadow of Political Cronyism
May 8, 2025 • Banking, All, Corruption, Economy, India, Laundering, Leaks, Originals
Indian public sector banks have been grappling with a significant NPA crisis, impacting the country's banking sector and economy. The crisis, fueled by political patronage,…
The Underbelly of Ujjwala LPG Scheme: Rural Women Bear the Real Cost of the Free LPG Scheme
May 8, 2025 • India, All, Commerce, Energy
Despite the ambitious goals of the Ujjwala LPG Scheme Yojana in providing free LPG connections to rural women, many beneficiaries are unable to afford refills,…